Im Defender for Endpoint und for Business kannst du für Ansichten und beispielsweise den Webfilter keine Gruppen oder Group-Tags aus Intune / Autopilot verwenden. Dazu musst du Eigene erstellen.
Wie du den Autopilot Group-Tag aber doch durgehend via Intune im Defender verwenden kannst, zeige ich dir in diesem Beitrag.
Mit dem Defender for Business kannst du die Scope-Tags zwar vergeben und für Ansichten nutzen, leider aber keine MDE-Gruppen erstellen.
Table of Contents
- Autopilot Group-Tag vergeben
- Dynamische Autopilot Gruppe
- Setup Intune Scope Tag
- Richtlinie zum verteilen des Tags auf die Geräte
- MDE-Gruppe aus Basis des Tags erstellen
Autopilot Group-Tag vergeben
Falls deine Geräte noch keinen Group-Tag haben, kannst du ihnen diesen in Intune zuweisen:
Intune > Devices > Windows > Windows enrollment > Devices
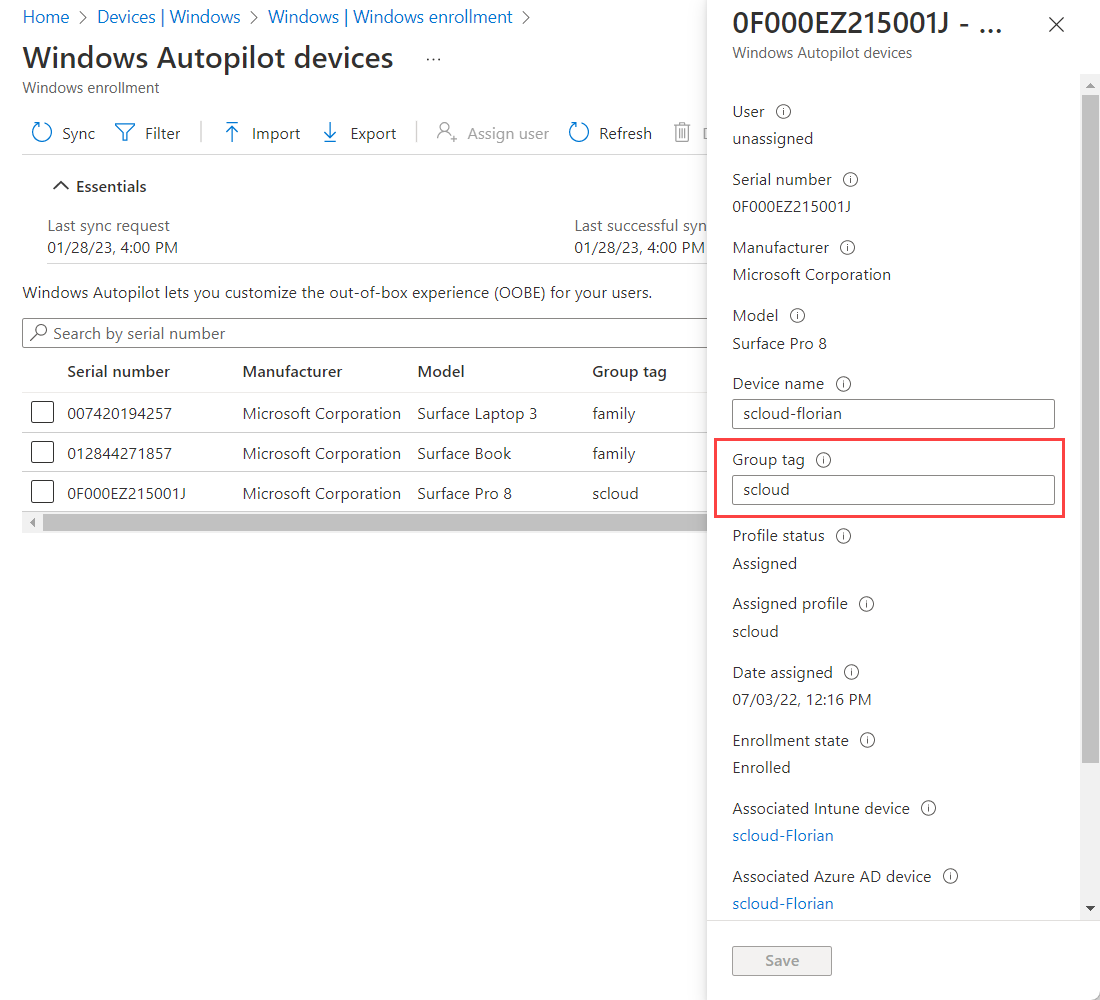
Dieser Group-Tag bleibt auch bestehen, wenn du ein Gerät zurücksetzt. Du darfst es nur nicht aus der Autopilot-Liste löschen.
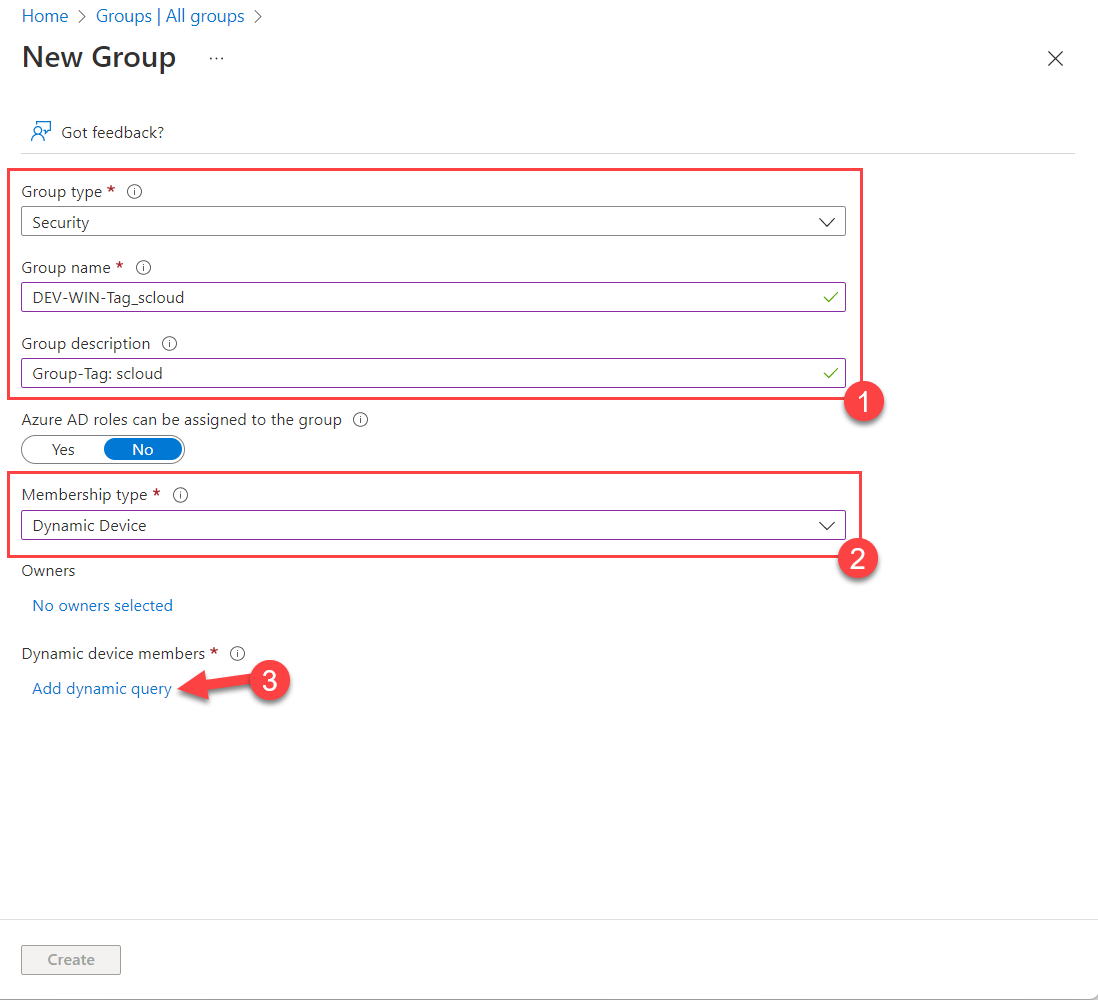
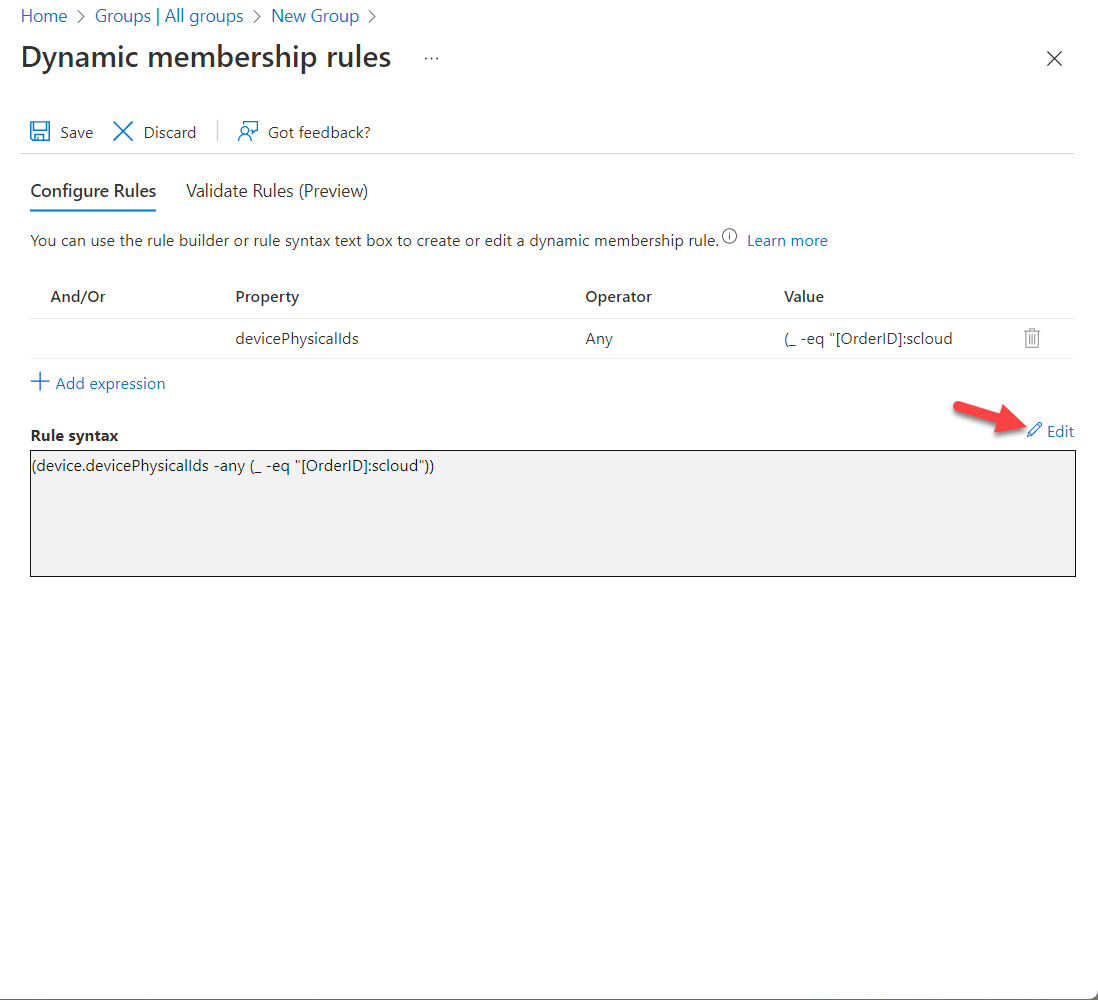
Dynamische Autopilot Gruppe
Um nun alle Geräte mit einem spezifischen Group-Tag in einer Gruppe zu haben, erstellen wir eine dynamische Gruppe, die genau diesen Group-Tag abfragt.
Die Query ist dabei: (device.devicePhysicalIds -any (_ -eq "[OrderID]:scloud"))
(Ersetze "scloud" mit deinem Group-Tag.)
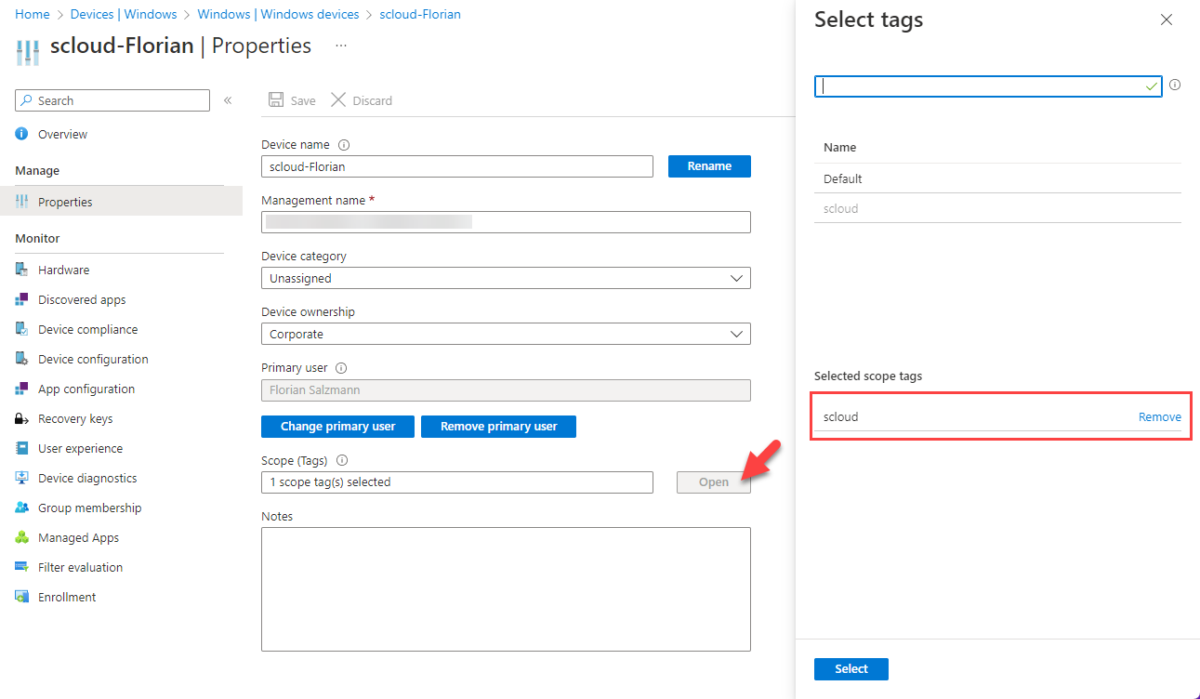
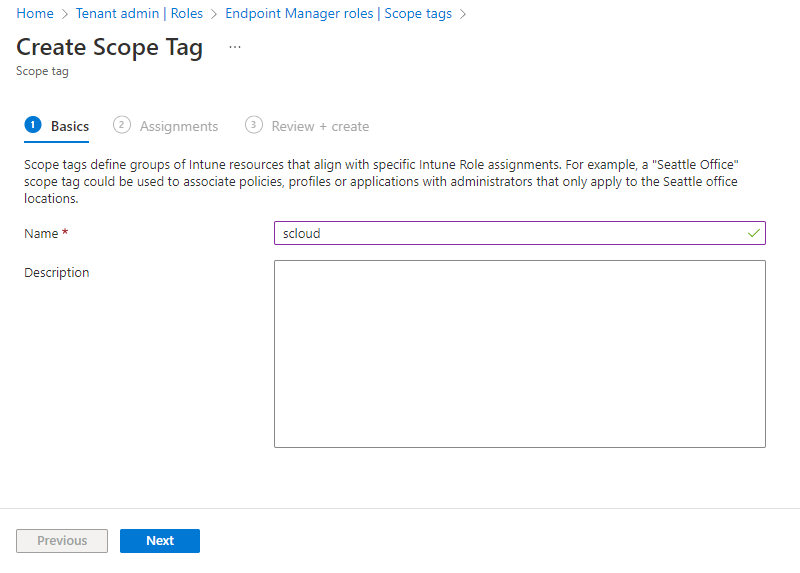
Setup Intune Scope Tag
Dieser Schritt ist nicht zwingend nötig, möchtest du aber die Tags konsistent überall sehen, empfehle ich ihn dir.
Mit den Intune Scope-Tags hast du zusätzlich die Möglichkeit, Berechtigungen auf einzelne Gerätegruppen und Richtlinien zu setzten. Dadurch kannst du beispielsweise einem Supporter nur Berechtigungen auf eine gewisse Abteilung geben. Alle anderen Geräte und Richtlinien wird er nicht sehen.
Erstellt werden Scope-Tags unter:
Intune > Tenant administration > Roles > Scope tags > + Create
Diesem vergeben wir nun denselben Namen wie zuvor. In meinem Fall "scloud".
Zudem weisen wir die erstellte dynamische Gruppe zu. So bekommen unsere Geräte mit dem entsprechenden Autopilot Group-Tag automatisch den Scope-Tag.
Nach der Zuweisung dauert es jeweils ein bisschen, bis der Scope-Tag zugewiesen ist. Ist er es aber einmal, siehst du das auf dem Geräteobjekt:
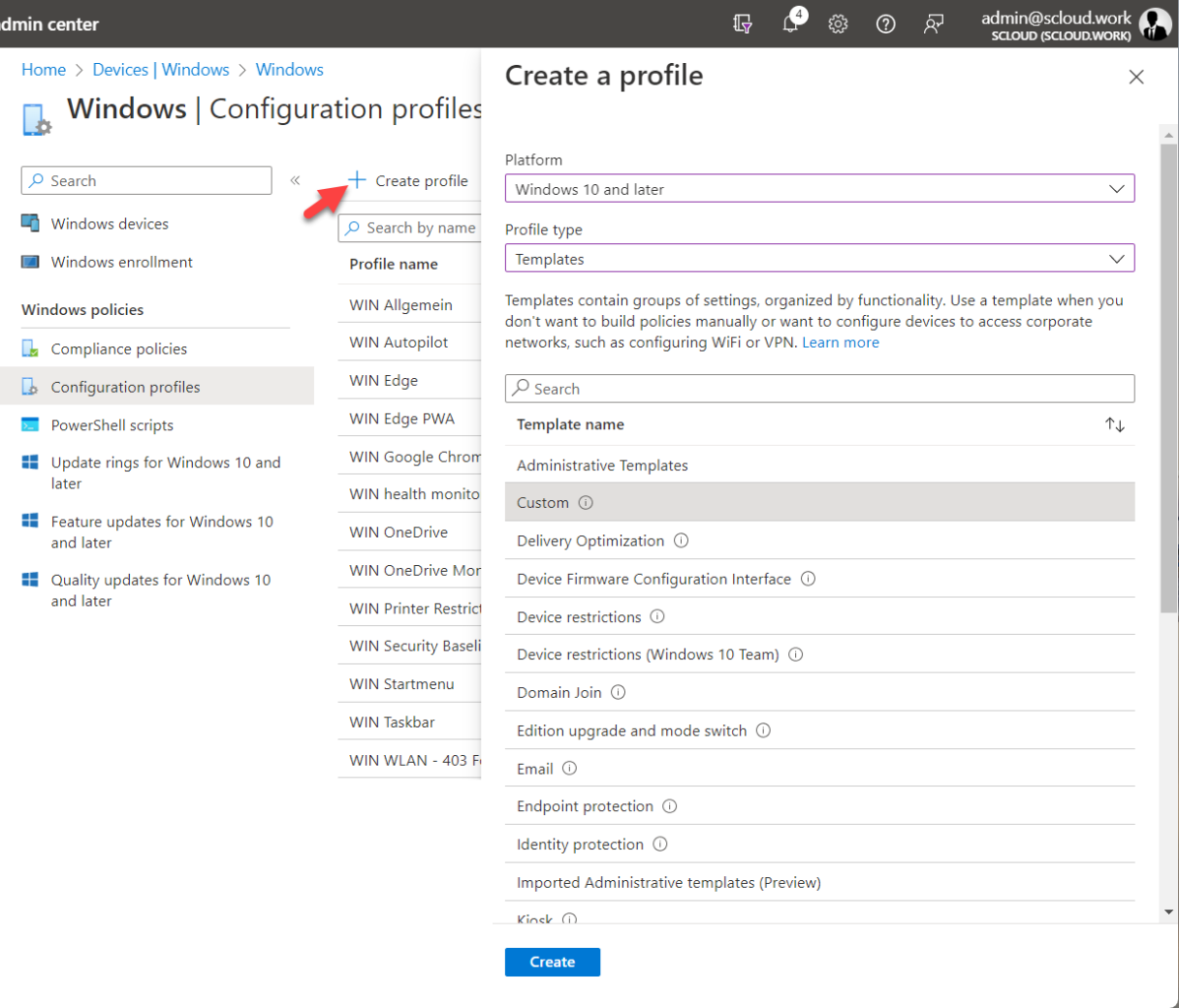
Richtlinie zum verteilen des Tags auf die Geräte
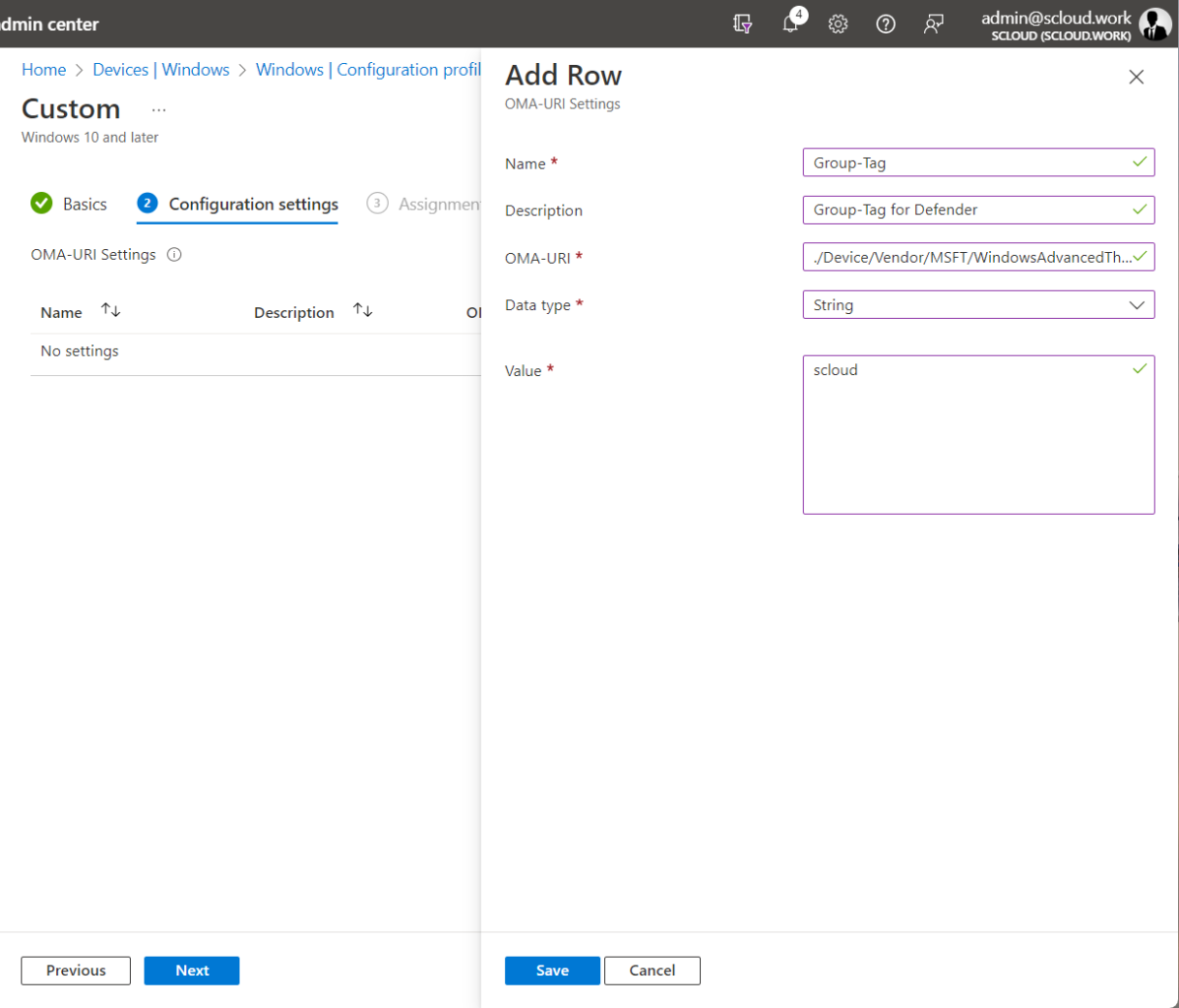
In Intune erstellen wir nun eine Custom-Policy mit einer OMA-URI. Diese vergibt den Tag dann dem Gerät lokal, von wo aus er wiederum im Defender for Endpoint / Business verwendet werden kann.
Achtung: Du kannst so pro Gerät nur einen Tag definieren.
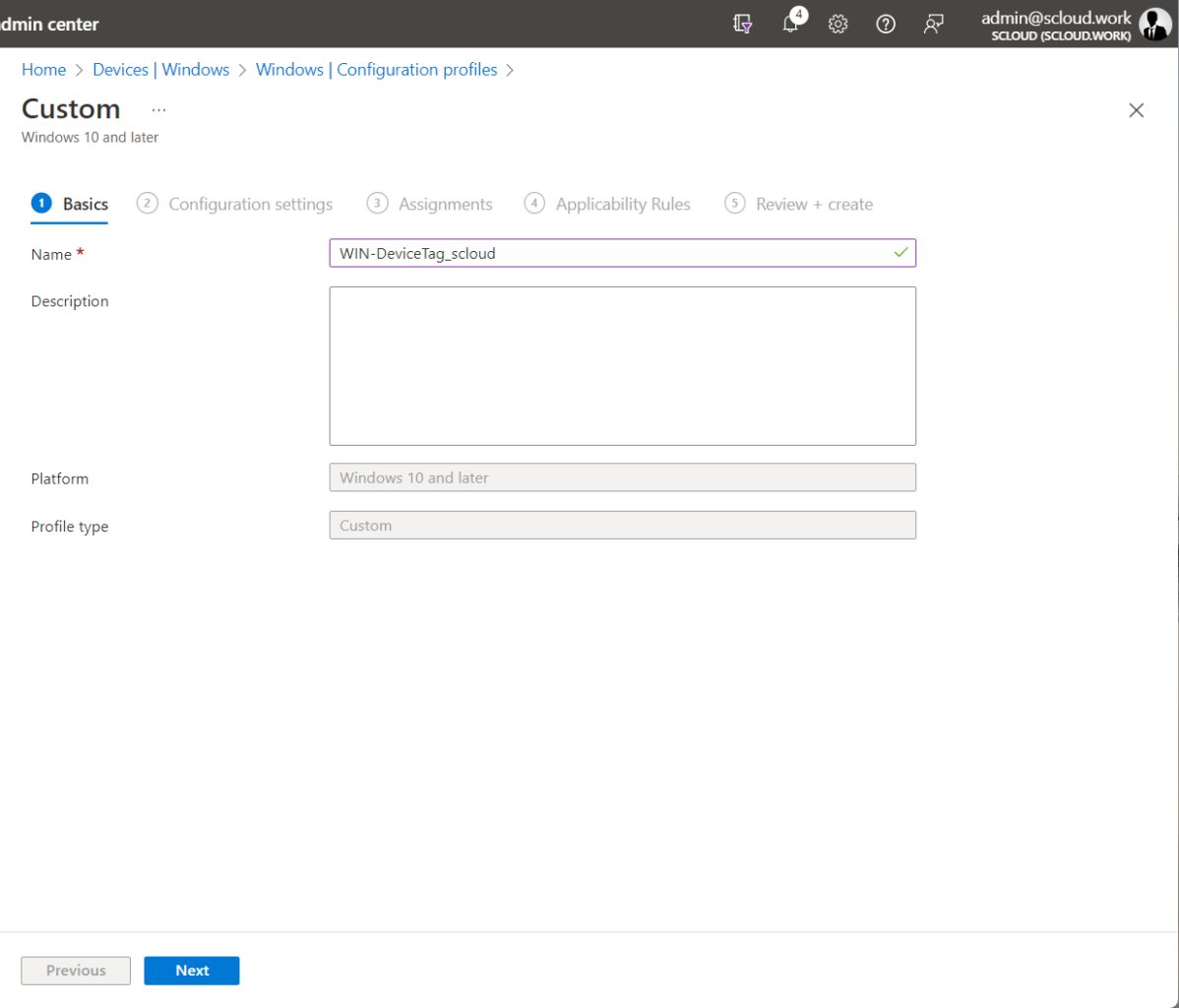
Intune > Devices > Windows > Configuration profiles > + Create profile (Windows 10, Templates, Custom)
Vergibt hier einen aussagekräftigen Namen und füge die nachstehende OMA-URI hinzu. Beim "Value" fügst du deinen Group-Tag ein.
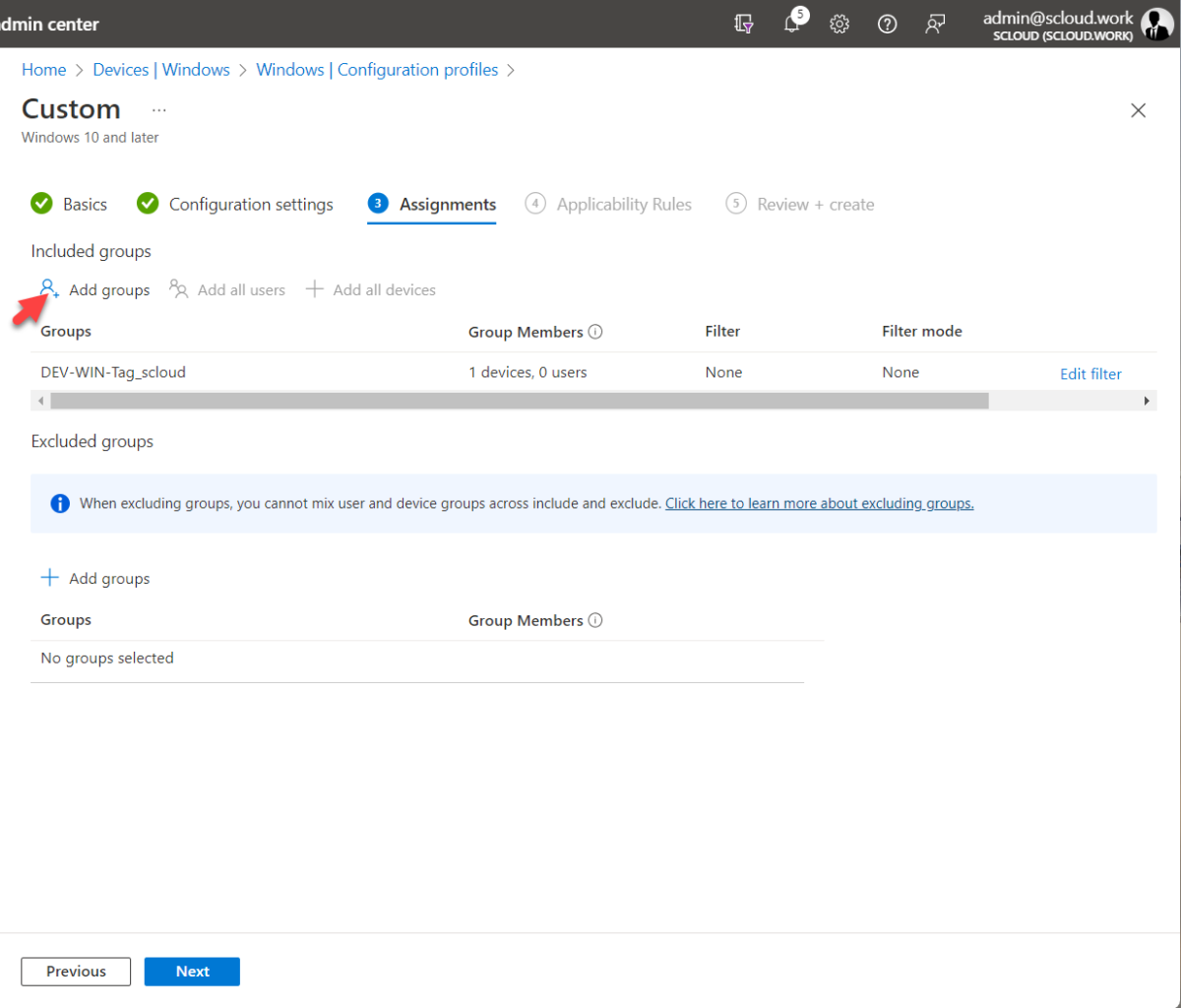
Die Richtlinie weisst du nun der zuvor erstellten dynamischen Gruppe zu.
| Name | Group-Tag |
| Beschreibung | Group-Tag for Defender |
| ORA-Uri | ./Device/Vendor/MSFT/WindowsAdvancedThreatProtection/DeviceTagging/Group |
| Data type | String |
| Value | scloud |
Mit etwas Geduld erscheint der Tag in der Geräteübersicht des Security Centers:
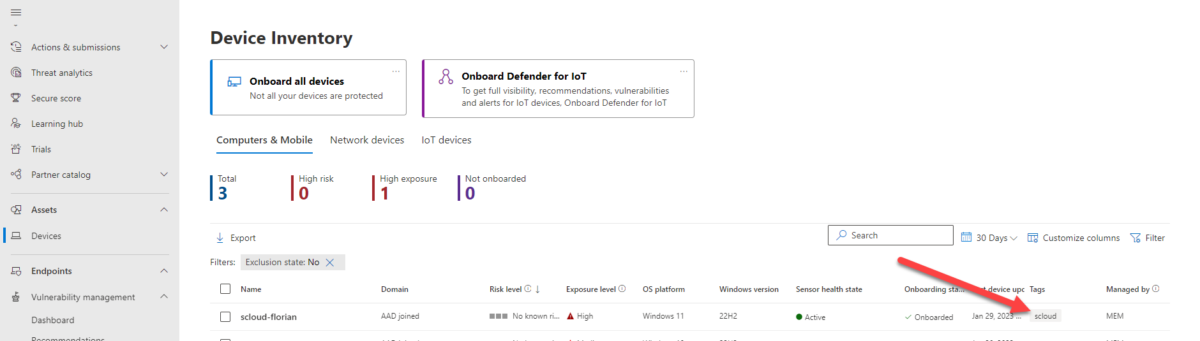
MDE-Gruppe aus Basis des Tags erstellen
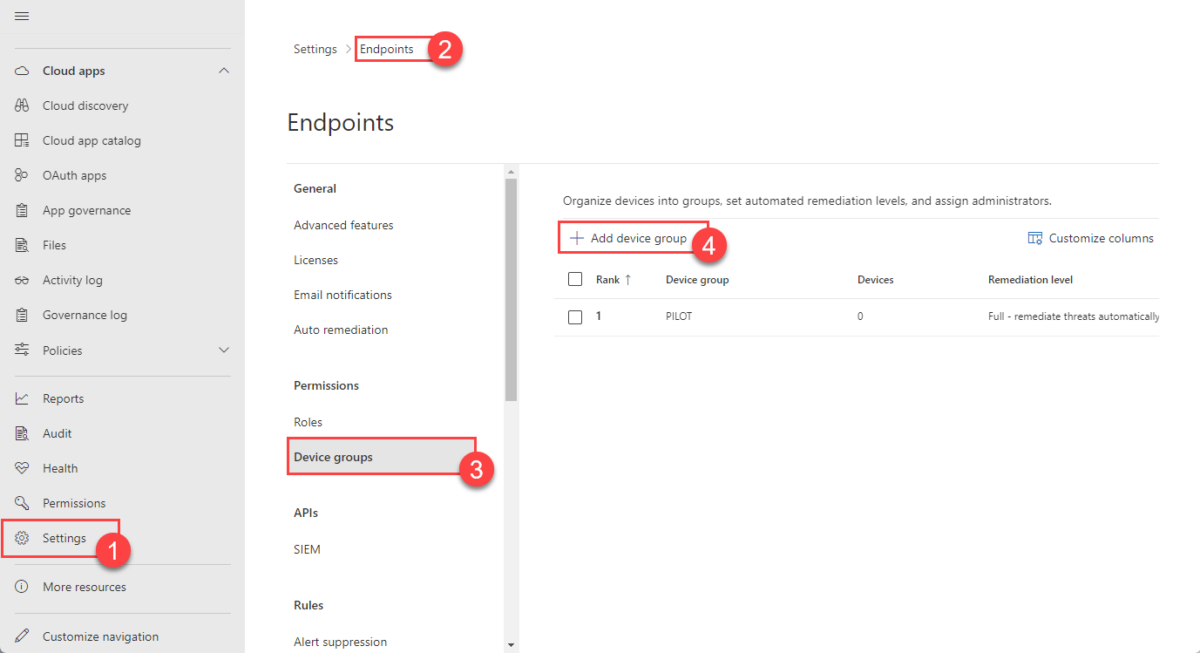
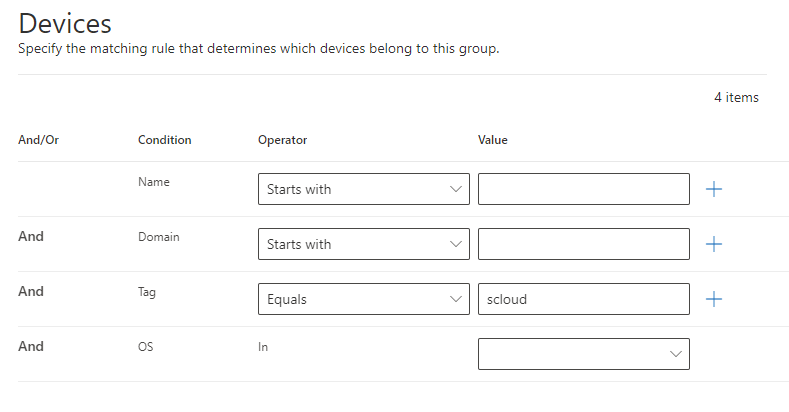
Nun, wo wir den Tag endlich im Defender haben, können wir eine Gruppe für diesen erstellen.
Diese Gruppe kann dann beispielsweise für Webfilter Richtlinien verwendet werden.
Dieser Schritt ist mit der Lizenz Defender for Business (Microsoft 365 Business Premium) nicht möglich.
MDE > Settings > Endpoints > Device groups > + Add device group
🏁 Und das wars, nun hast du den Tag von Autopilot über Intune bis hin zum Security Center / MDE.






1 Response
[…] Wie die Scopes funktionieren und wo du sie erstellen kannst, habe ich dir hier zusammengestellt:Defender for Endpoint Scope-Tag via Intune | scloud […]