Wird ein Gerät von Dell neu geliefert, sind die Treiber meistens aktuell. Nach einem Jahr, oder falls das Gerät einmal neu aufgesetzt wird, fehlen schnell Treiber oder sind nicht mehr auf einem aktuellen Stand. Das kann Sicherheitslücken öffnen oder dem Enduser Probleme verursachen. Um genau solle Situation zu vermeiden, verteile ich mit Intune das Programm "Dell Command Update" über welches ich dann via Proactive Remediations die Treiber von Dell regelmässig überprüfe und updaten / installieren.
Updated, 10. Mai 2023 - Dell Command Update Version 4.9
Table of Contents
- Filter für Dell-Geräte erstellen
- Dell Command Update
- Proactive Remediations Paket erstellen
- Proactive Remediations Report
Filter für Dell-Geräte erstellen
Bevor wir mit der Verteilung beginnen, erstellen wir noch einen Filter für Dell-Geräte.
Dies machst du unter: Tenant Administration > Filters
Dem Filter geben wir einen aussagekräftigen Namen und wählen als Plattform "Windows 10 and later".
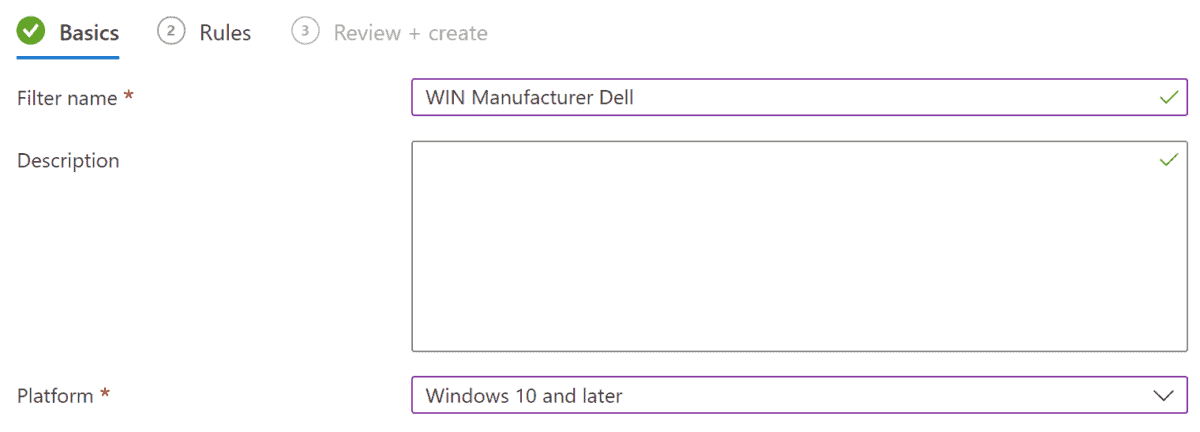
Als Filter Regel nehmen wir lediglich den Hersteller "Dell".
Zur Prüfung des Filters kannst du auf die Preview des Filters klicken.
(device.manufacturer -eq "Dell Inc.")
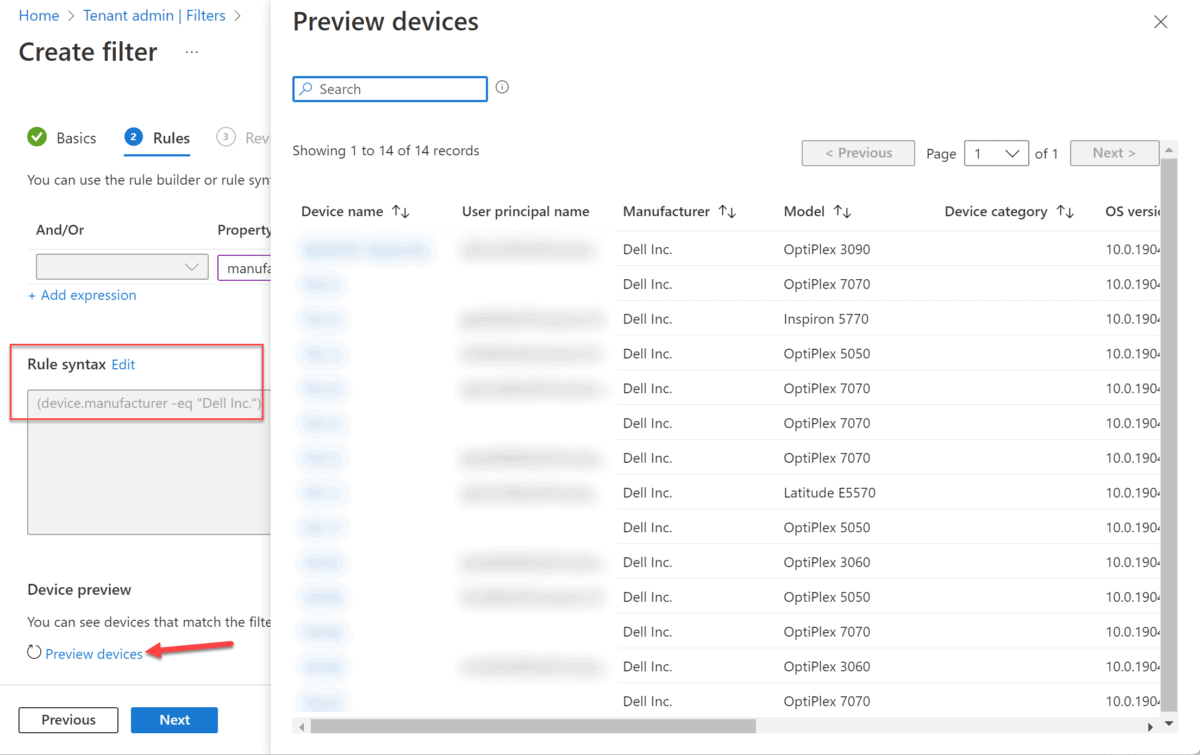
Nach einem Klick auf "weiter" und "Erstellen" ist die Erstellung des Filters bereits abgeschlossen. Diesen benötigen wir später wieder, um das "Dell Command Update" nur auf Dell-Geräten zu installieren.
Dell Command Update
Um die Prüfung via Proactive Remediations anstossen zu können, muss zunächst das Programm "Dell Command Update" installiert werden. Dazu habe ich dir auf GitHub das fertige Win32 Paket bereitgestellt.
Das Paket beinhaltet die EXE mit der Version 4.9.0.
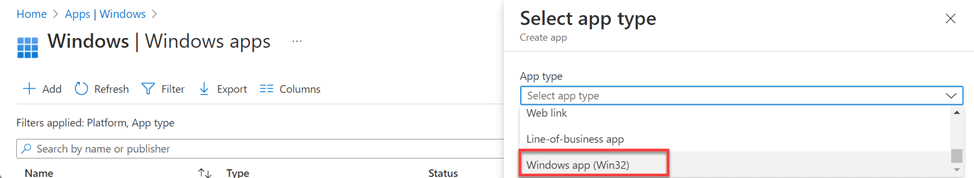
Dell Command Update via Intune installieren
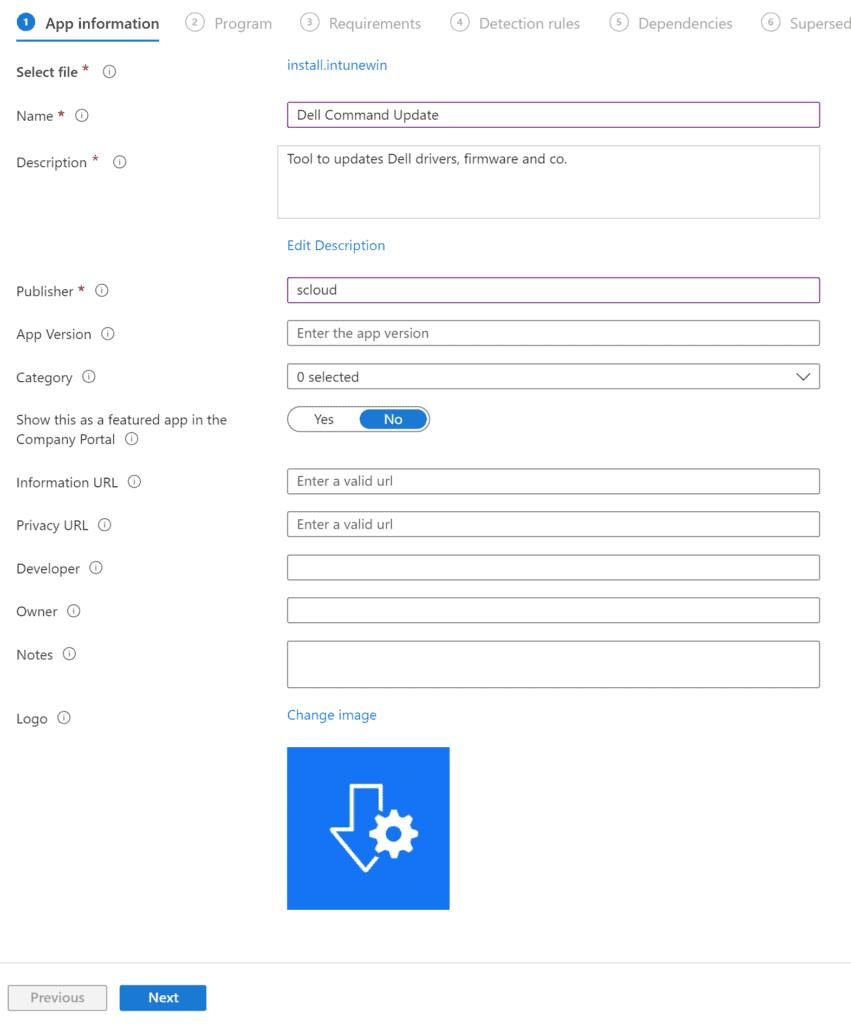
Für die Verteilung mit Intune navigiertest du zu «Apps > Windows», wählst «+Add» und «Windows app (Win32)».
Anschliessend lädst du die Datei "install.intunewin" hoch.
In den «App Informationen» füllst du den Namen, die Beschreibung und den Herausgeber ab.
Ein Logo habe ich dir ebenfalls auf GitHub zur Verfügung gestellt.
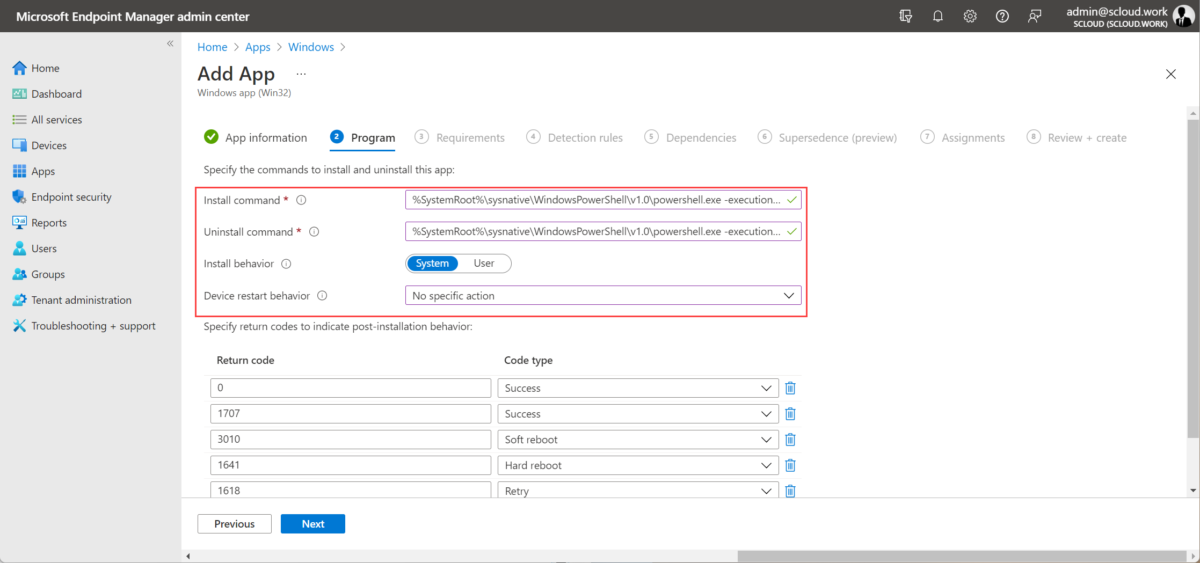
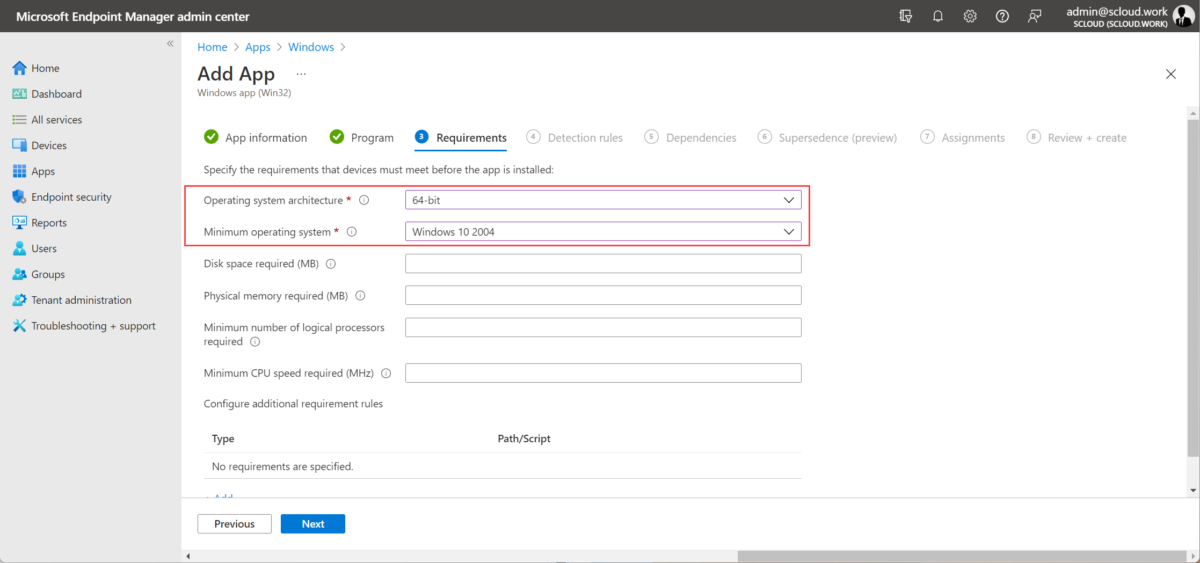
In den nächsten Schritten fügst du die Installationsparameter wie unten aufgelistet ein uns setzt die Anforderungen.
| Install command | %SystemRoot%\sysnative\WindowsPowerShell\v1.0\powershell.exe -executionpolicy bypass -command .\install.ps1 |
| Uninstall command | %SystemRoot%\sysnative\WindowsPowerShell\v1.0\powershell.exe -executionpolicy bypass -command .\uninstall.ps1 |
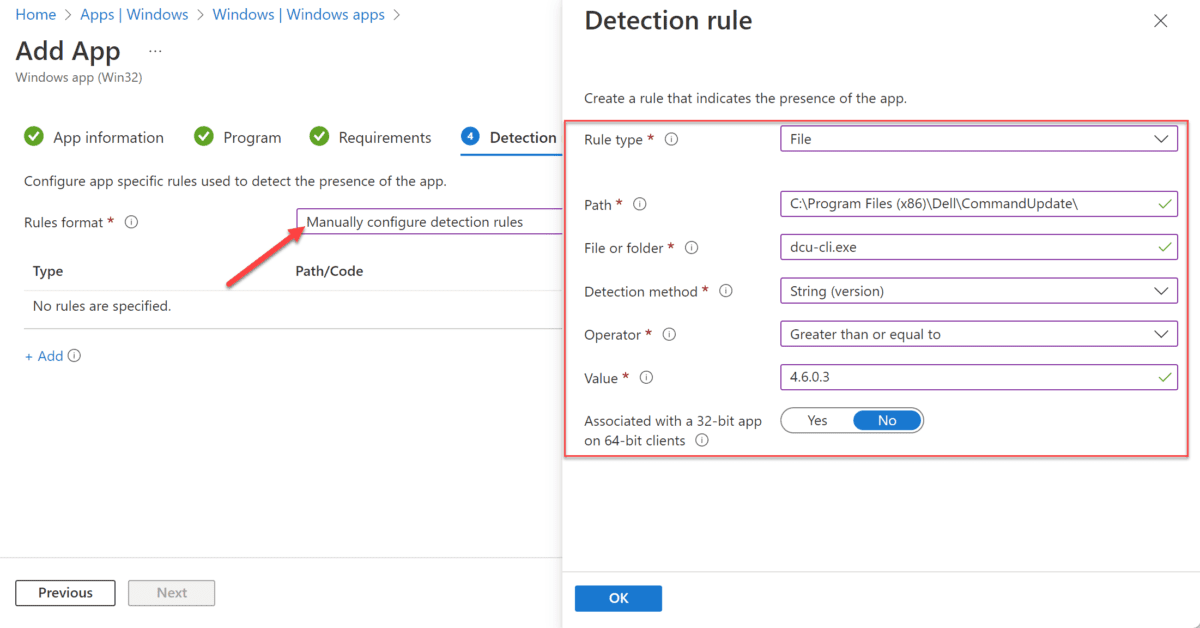
Bei der Erkennungsregel fügst du eine Manuelle mit folgenden Parametern hinzu:
File, Sting (version):
- C:\Program Files (x86)\Dell\CommandUpdate\
- dcu-cli.exe
- 4.6.0.3
Den Schritt "Abhängigkeiten" und "Supersedence" kannst du überspringen.
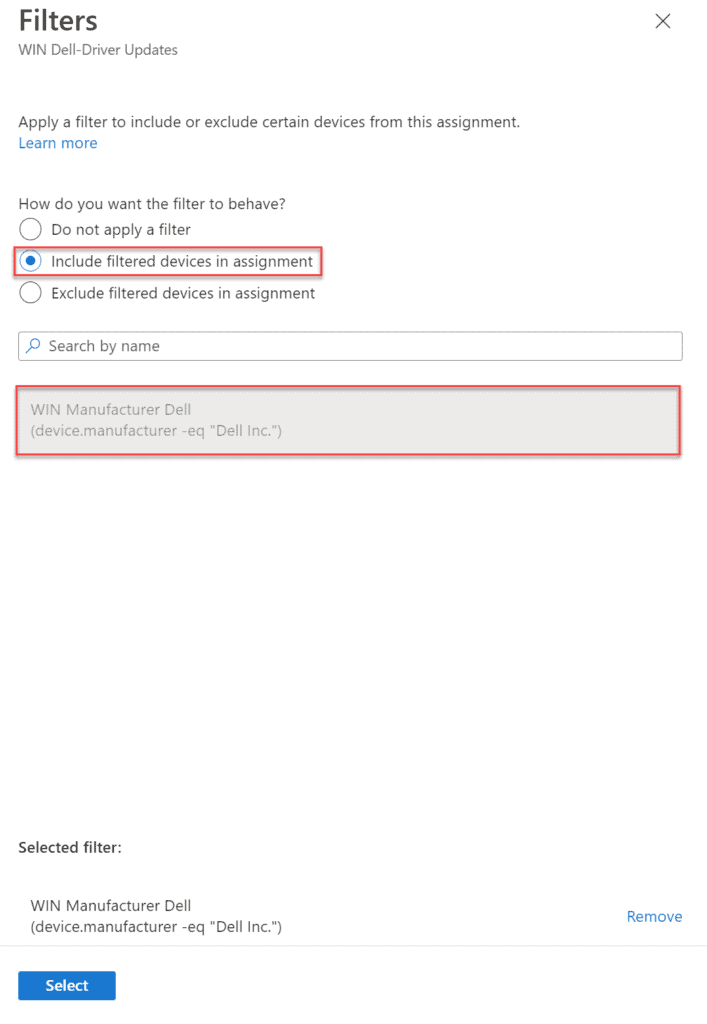
In der Zuweisung weisst du nun eine Zielgruppe zu. Dabei kann diese auch alle Geräte beinhalten. Dass aber nur Dell-Geräte das Programm erhalten, wenden wir zusätzlich den im ersten Teil dieses Blogs erstellten Filter an.
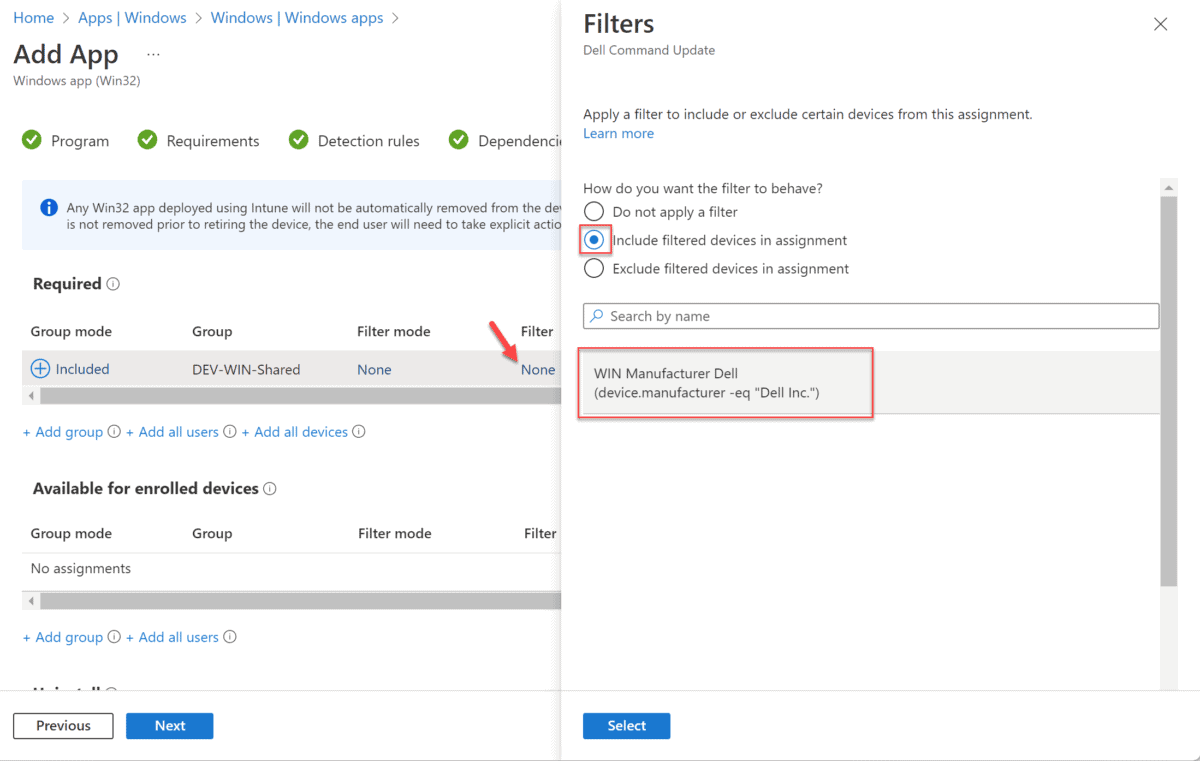
Proactive Remediations Paket erstellen
Mit der Installation des "Dell Command Update" haben wir die Voraussetzungen erfüllt und können das Proactive Remediations Paket erstellen.
Wie gewohnt habe ich dir die Scripts auf GitHub abgespeichert:
Falls du keine Windows Enterprise oder Education Lizenz hast, kannst du diese Funktion nicht nutzten.
Eine Alternative zeige ich dir hier: "Proactive Remediation for Business" | scloud
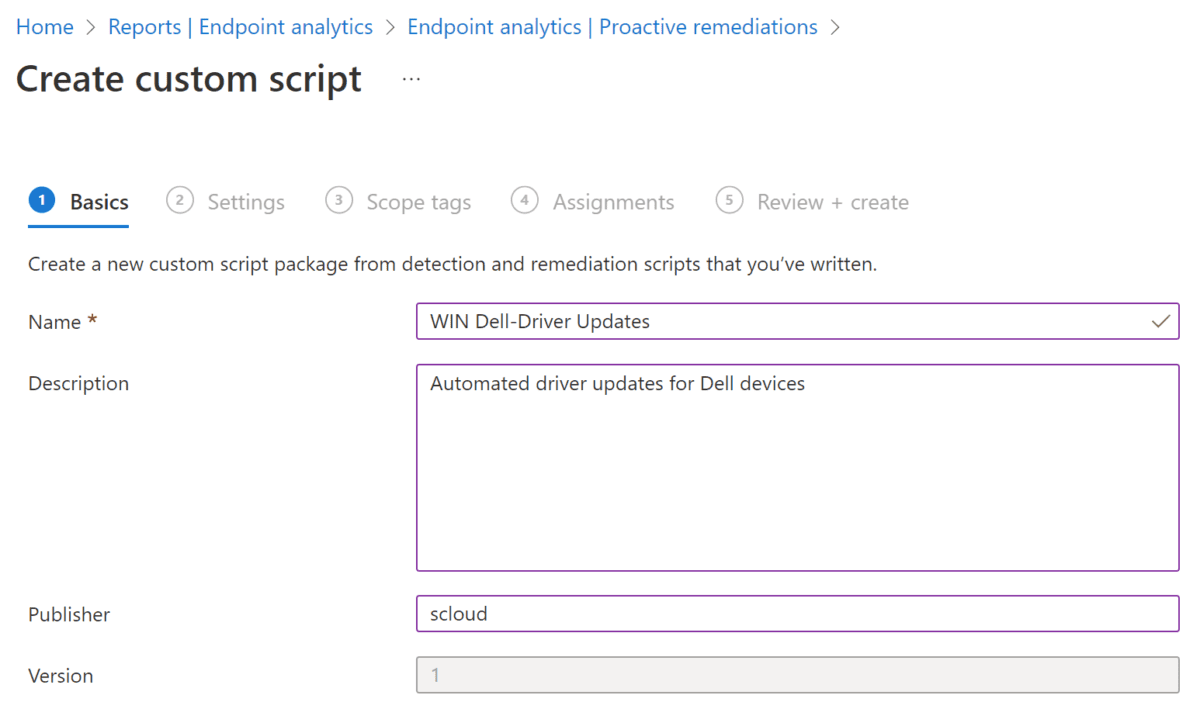
Als erstes musst du ein neues PR-Paket erstellen:
Reports > Endpoint analytics > Proactive remediations + Create script package
Diesem gibst du einen Namen.
Anschliessend lädst du die das Detection- und Remediation-Skript hoch.
In meiner Vorlage werden Treiber und Firmware Updates installiert, falls du nur Treiber möchtest, kannst du einfach in der 4. Zeile der beiden Scripts nur die "Drivers" eintragen.
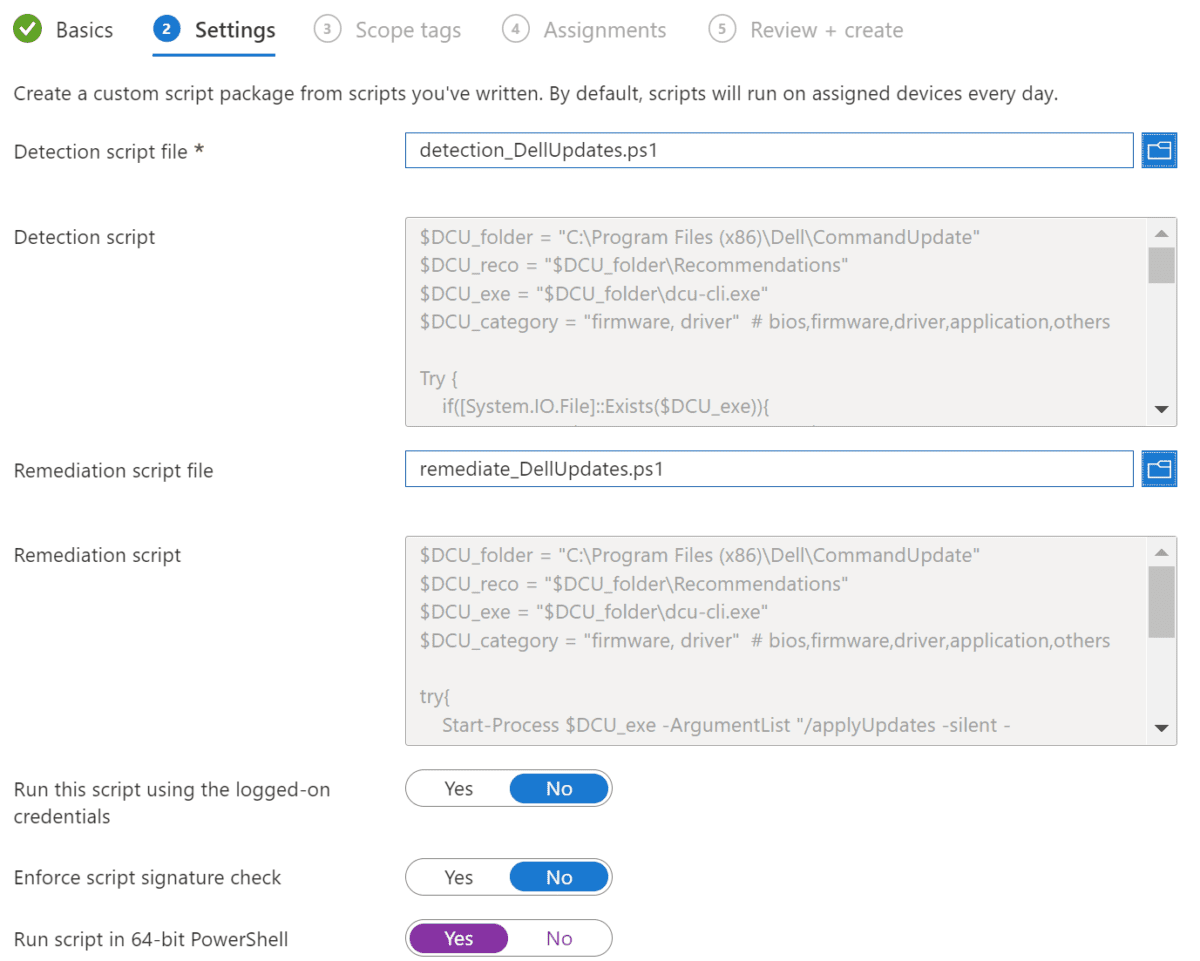
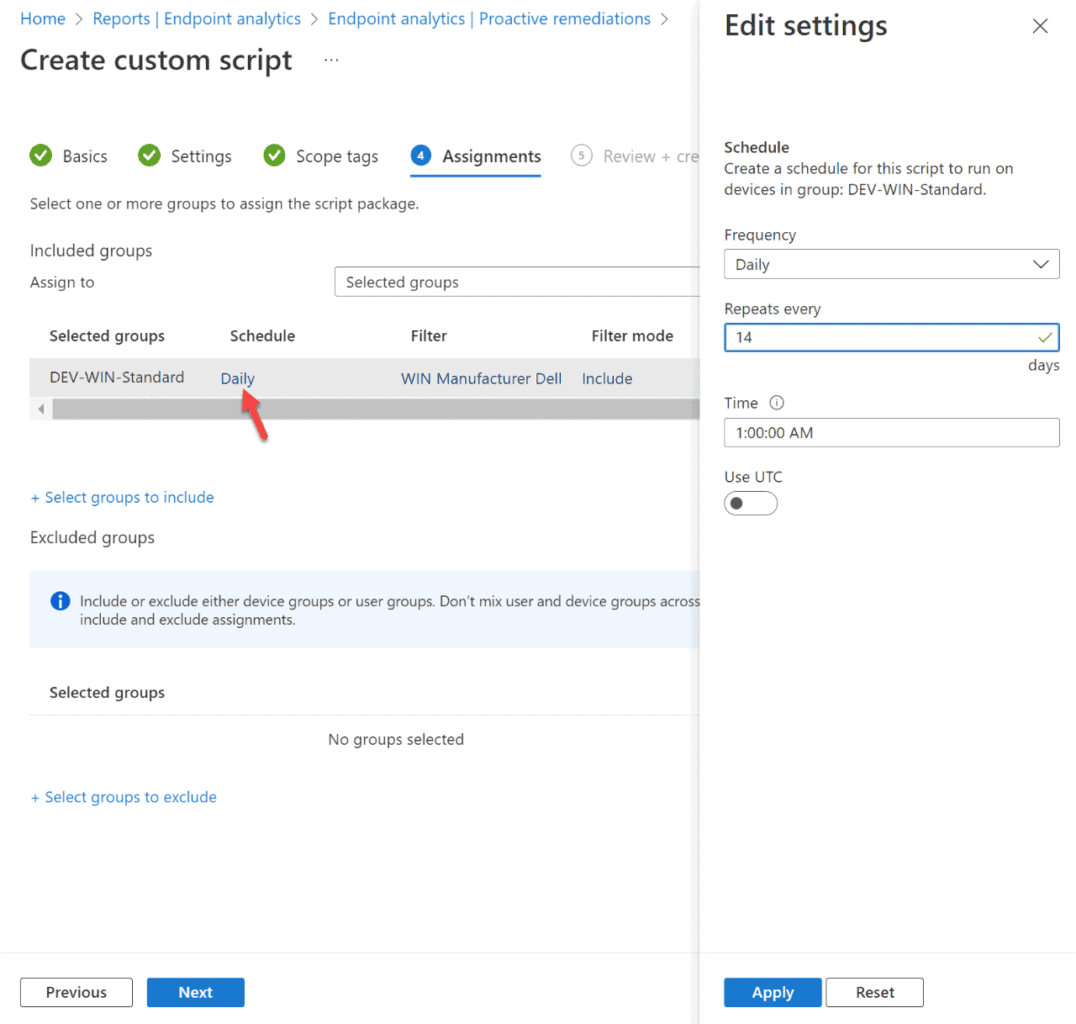
In der Zuweisung wählst du eine Gruppe aus und definierst auch gleich das Intervall der Prüfung dieser.
Ich habe dazu alle 14 Tage gewählt. Wenn das Gerät zu diesem Zeitpunkt nicht läuft, wird das Script beim nächsten Start ausgeführt.
Zusätzlich wenden wir auch hier wieder den Filter für die Dell-Geräte an.
Das wars, jetzt werden die Treiber deiner Dell Geräte regelmässig via Endpoint Manager / Intune aktualisiert.
Proactive Remediations Report
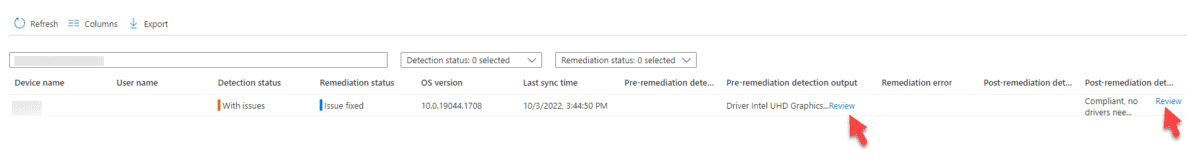
Bei der Ausführung von Detection und Remediation werden die Outputs an den Microsoft Endpoint Manager gesendet und können dort eingesehen werden.
Dazu müssen bei der Ansicht jeweils die zusätzlichen Spalten angezeigt werden. Das kannst du im entsprechenden PR-Paket über die Schaltfläche "Columns" machen.
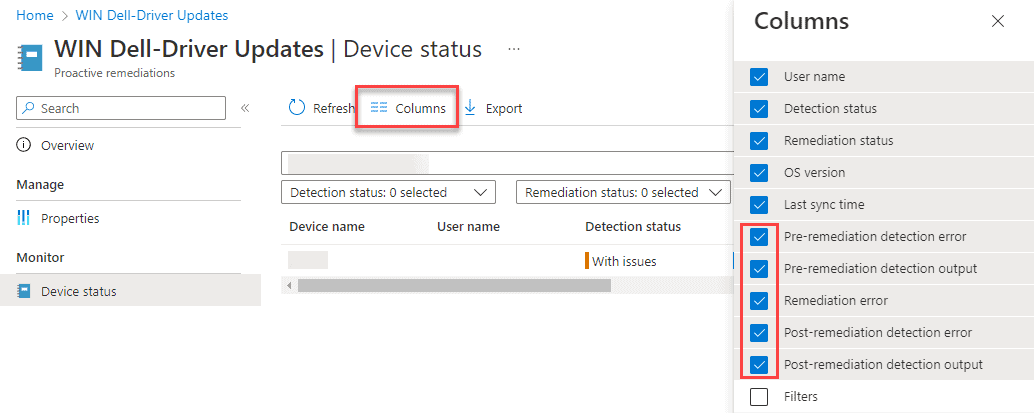
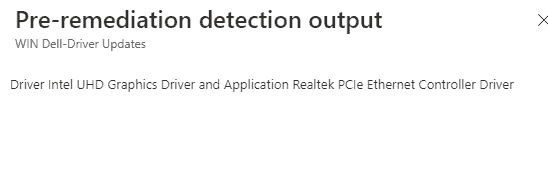
Klicks du anschliessend auf die entsprechenden "Review" Links, werden dir beispielsweise die benötigten Treiber angezeigt:





Hi,
thanks for this great tutorial.
I have various doubts... Do we have to install Dell-Command-Update-Application_T97XP_WIN_4.6.0_A00.EXE and both scripts (install.ps1 and uninstall.ps1)?
Thanks!
You're welcome!
No, you only have to upload the "install.intunewin" which contains all files.
The "install.ps1" then calls the exe for the silent installation process. The "uninstall.ps1" is only executed if you decide to uninstall the app via Intune.
You have to add it to your netlogon folder where everyone has Read access and then use the below for the install and uninstall scripts:
%SystemRoot%\sysnative\WindowsPowerShell\v1.0\powershell.exe -executionpolicy bypass -File "\\YourNetworklocation\NETLOGON\Dell-Command-Update\DCU-Intune\install.ps1"
%SystemRoot%\sysnative\WindowsPowerShell\v1.0\powershell.exe -executionpolicy bypass -File "\\YourNetworklocation\NETLOGON\Dell-Command-Update\DCU-Intune\uninstall.ps1"
Otherwise Intune won't know where to look for the install and un-install files.
Cheers
If you use a win32 app, the intunewin will be "unzipped" on the target machine and all the sources will be available on the local machine. So you don't have to add a network share and can deploy it regardless of the network location.
A UNC Path is only necessary if you use another solution than Intune to deploy the software.
Ok,
so... All the Dell updates will be installed silent in all devices?
Correct, with the provided script all Dell driver and firmware updates.
So what's the process/work-around for the proactive remediation if we don't have the appropriate licensing for that? We only have 365 business premium and do not have any of the E3/E5/A3/A5 that it requires to run proactive remediation.
For that you can use the method described in my blog post "Proactive Remediation for Business": https://scloud.work/proactive-remediation-for-business
Thank you for this guide. I ran through it and was able to get things working properly in the end. The one thing that didn't work for me from your code was the update.count if/else in the detection script. Running $DCU_analyze.updates.update.count always produced 0 for the count, even if I have output in the xml and when I output the value on $DCU_analyze.updates.update. I still need to test this fully, but my initial changes made it work for me and reports back to remediation with the pending updates. I added "$var = $DCU_analyze.updates.update | Measure-Object" below the $DCU_analyze test-path and then changed the count in the if statement to "$var.Count -lt 1". No other changes in the scripts besides adding the bios flag to the check and it's now running in my qa environment.
The 2 scripts how do you bypass execution policy if Dell Command was already installed?
Hi Rick, I'm not sure where you referring to. Do you mean the PR scripts?
Those are executed by the IMExtention and don't need special execution policies.
Hi Florian
Excellent article. Dell have released version 4.7 of Dell Command, what are the steps to create an updared install.intunewin file?
Also we are a all Dell house so in theory I could skip the use of Filtering of the devices?
You can do so by downloading the "Dell Command Update.zip" from GitHub, unzip and replacing the EXE.
In addition, you must change the EXE-Filename in line 12 of the install.ps1. after that you can create the intunewin (https://scloud.work/win32-app-intunewin/) and upload the newest version.
Don't forget to also increase the version in the detection rule.
Regarding the filtering, not necessarily, but I would do so... cause you never know if there will be another device.
With the newest version of the Dell Command Update (4.7.1), Dell has removed the previous style and only uses the UWP version. However, UWP now works with CLI but the installation is in Program Files and not Program Files (x86).
Thanks for the info, will add that to the post!
Looking at the updated version 4.8.0 , I see there is also regular version and not only UWP, can I use this version ? https://www.dell.com/support/home/en-il/drivers/driversdetails?driverid=714j9
Thanks for the tip, it's true. I have updated the package to the latest version.
Excellent work. Just tested it in my test environment and working as expected.
However, can we include a line in it to suspend bitlocker, for the firmware upgrade, or else it will ask for the Bitlocker key when booting up the computer.
unfortunately I don't have a solution for that now.
Buenas tardes,
Me parece genial lo que has hecho con esto, lo estoy probando en el ambiente del cliente.
pregunto?
En la remediación se podría colocar este parametro:
Start-Process $DCU_exe -ArgumentList "/configure -silent -autoSuspendBitLocker=enable -userConsent=disable" -WaitHola Martin, Thanks a lot for your input!
Just tested and updated the remediation file with your config parameter.
Which line was this injected in? Is this a temporary disabling during the patching process?
It's in line 7. And correct it does, so the user does not have to fill in the recovery key.
Hi Florian,
Excellent scripts and they appear to work great.
How is the functionality with BIOS firmware updates if Bitlocker is enabled? Checked a few of my devices today and they have installed various firmwares and drivers, but all have the BIOS update sitting.
I excluded them. Cause it can cause a lot of troubles in combination with BitLocker
Hi,
The install.intunewin file autofills install.ps1 as the App name, not Dell Command update like in the screen shot. Does that matter? I know i can edit the name of the app but wanted to be sure it's going to create correctly as an application.
Thanks
At the upload Intune uses just the filename, you can set the name to "Dell Command update" or whatever you like. The Name doesn't matter about the installation.
What with reboots? if anybody will get this upgrade it will reboot automatically? without prompt?
It won't reboot automatically; the installation waits until a regular reboot is triggered.
Hello,
I have a problem. The detection script find drivers, prepare .xml log, but ?the remediate script not run?, because the remediation status: Recurred. - I used just driver update, don't firmware in the script.
What can be the solution?
I used newest and oldest script, same problem.
Dell Command update verion: 4.6.0
I just got some input from the field and readers and updatet the detection. Maybe the new detection can help in your case as well.
Hi Florian
Thanks for your work on automation for dell with dell command update.
I'm going to put it in production soon on a 2000 computer park
I tested on a group of 10 computers and all return a value of compliant (0 drivers).
While I have drivers available on the computers.
Looking at your code on the detection part line 11 - 19 I still have the number of node at zero
I modified this part in the following way which shows me the number of nodes in the XML file
if(Test-Path "$DCU_report\DCUApplicableUpdates.xml")
{
[System.Xml.XmlDocument] $data = new-object System.Xml.XmlDocument
$data.load("$DCU_report\DCUApplicableUpdates.xml")
$rows=$data.selectnodes("//updates/update")
}
if($rows.Count -lt 1){
Write-Output "Compliant, no drivers needed"
Exit 0
}else{
Write-Warning "Found drivers to download/install: $($rows.name)"
Exit 1
}
Thanks for that, got another hint on GitHub regarding that and updated the detection 🙂
Hi,
Thanks for all the workaround but in my tenant it seem that the drivers doesn't want to be updated they all fall into the recurred but the issue doesn't seems to be resolved.
Could you check what happens, if you run the update command manually (as admin) on one of the affected machines?
So I've done this,
Running the script within the system activates the dellcli executable and identifies the dell drivers to install ( which it had been for me without using the CLI prior ) , and all it does is resolve 17 where it writes the red WARNING: and lists the drivers that need to be installs.
It then shuts down the script, performing the EXIT function and nothing happens.
Thank for your great work.
I'm having issues with the drivers actually installing.
The script provided is returning with reoccurring errors.
Firmware and Dell Apps are successfully installing; however, drivers have not been.
I have the device set to run the script hourly and it's powered-plugged in.
Hello Andrew T
I've got the same issue, the scan is made perfectly but the drivers doesn't apply.
On intune it says that the devices loop on reoccurring error.
it's set to hourly also and power-plugged
The issue seems to be from this line...
Start-Process $DCU_exe -ArgumentList "/applyUpdates -silent -reboot=disable -updateType=$DCU_category -outputlog=$DCU_report /configure -silent -autoSuspendBitLocker=enable -userConsent=disable" -Wait
If you remove "/configure -silent -autoSuspendBitLocker=enable -userConsent=disable" it works just fine. Deos the CLI arguments support applying updates and doing configuration changes at the same time?
A better option would likely be having 2 seperate commands:
Start-Process $DCU_exe -ArgumentList "/configure -silent -autoSuspendBitLocker=enable -userConsent=disable" -Wait
Start-Process $DCU_exe -ArgumentList "/applyUpdates -silent -reboot=disable -updateType=$DCU_category -outputlog=$DCU_report" -Wait
Another thing to consider is that if you update the Dell Command Update from 4.6.0 to 4.7.1, it can move the CLI command from "Program Files (x86)" to the 64bit "Program Files"
Hi Patrick,
Your workaround is the fix, i came to the same conclusion as DCU came with this error message when i ran it from the prompt
-------------------------------------------------------
Duplicate commands provided.
The program exited with return code: 103
-------------------------------------------------------
Hence i don't believe that DCU is so happy about dual commands in one line.
wondering if anyone had solutions for the script scanning but not actually installing the device drivers?
Hi,
with addition of Bitlocker suspension line, can BIOS updates be enabled without causing issues?
Hello,
When I ran the script it returned several of the following errors:
The ampersand (&) character is not allowed. The & operator is reserved for future use; wrap an ampersand in double quotation marks ("&") to pass it as part of a string.
Any help would be greatly appreciated!
I was able to figure out what I was doing incorrectly.
if the PCs already have the Dell command update with old version (4.5) do i still need to update the Dell command update to the latest version via intune?
Not necessarily. But it's always good to keep your software up to date.
Hi All
This article has been great help and I was able to create fully automated process. However, now I have got stuck.
We have BIOS password enabled on all our organisation laptops. And because of which it seems remeidation script is not able to push BIOS update.
I tired rebooting the test device few times and eveytime it comes back with same number of updates pending.
Is there a way to automate and put BIOS password settings in the remediation script.
Thanks
It should work with the
/configure - autoSuspendBitLocker=enableparameter.Here's the reference article from Dell: https://www.dell.com/support/manuals/de-ch/command-update/dellcommandupdate_rg/dell-command-update-cli-commands
Thanks for this Florian.
I've done all the work with Intune and I can see this is working to a degree. A laptop I'm working with has installed 'security' updates, but not done any 'critical firmware' updates. Although in remediation it's reporting : "Without issues, compliant."
Does this do firmware updates? It appears to update the firmware on docking stations.
Further to my previous message Florian - it appears that system BIOS isn't being updated, but something like the Dell dock 'firmware' is.
I've manually ran the script for detection and what I've seen is that on a laptop where there is a bios update available through DCU and running the GUI, it currently doesn't detect it.
However, if you edit the line in detection to include BIOS:
$DCU_category = "firmware,driver,bios"
It will now detect a BIOS update.
I'm presuming adding 'bios' to detect and remediate should resolve this issue. Perhaps DCU has been updated to separate 'bios' and 'firmware'.
Thats correct, I usually exclude BIOS cause of some troubles with BitLocker.
Thanks for this!
In the remediation script, if you were to add application to the category list I assume this would keep Dell command up to date then?
It could be, I haven't tested it. Because sometimes in the DCU updates the commands change, so I prefer to do the DCU update on my own.
Hi
we would like to block certain Dell drivers from installing. Would this solution be able to do that?
Do you mean specific categories or specific drivers?
It would only be possible to block categories.
Hey,
Does the proactive remediations still work for you?
When I manually run dell command updates it detects a few critical and recommended updates. but the remediations says there's nothing to update?
Thanks
Aras
Unfortunate I don't habe my Dell anymore (Mainboard died).