Mit einem FIDO2 Key, wie z.B. dem YubiKey Bio, kann die Passwortlose-Authentifizierung an Microsoft 365/Azure AD und auch an Windows Geräte realisiert werden. Dadurch kann eine Organisation gerade für Produktionsmitarbeiter einen Schritt Richtung "Passwordless" gehen.
Die Firma yubico bietet mit ihren YubiKeys verschiedene Möglichkeiten den Ansatz einer passwortlosen Umgebung zu verfolgen. Als "Passwordless" zählt dabei die Authentifizierung mit einer Smart-Card, einem PIN oder einem biometrischen Faktor. Die YubiKeys mit dem FIDO2 Standard lassen sich in vielen verschieden Applikationen nutzen, unteranderem auch im Microsoft 365/Azure Universum.
Eine schöne (Marketing) Zusammenfassung dazu findest du auf Passwordless login with YubiKey (yubico.com). Übersicht aller Unterstützten Applikationen für MFA und/oder Passwordless: Works with YubiKey catalog | Yubico
Der neue YubiKey Bio Series vereint endlich die bekannte Smart Card Funktion mit einem Fingerprint. Dadurch ist bei einem Login via YubiKey keine PIN mehr nötig.
Ich konnte den Key einige Zeit testen und bin zufrieden, wie wenig ich meine Tastatur für meine allgemeinen Arbeiten benötige. Dies genauso an fremden Geräten.
Table of Contents
Demo Video
Voraussetzungen
im Tenant um einen YubiKey zu nutzen
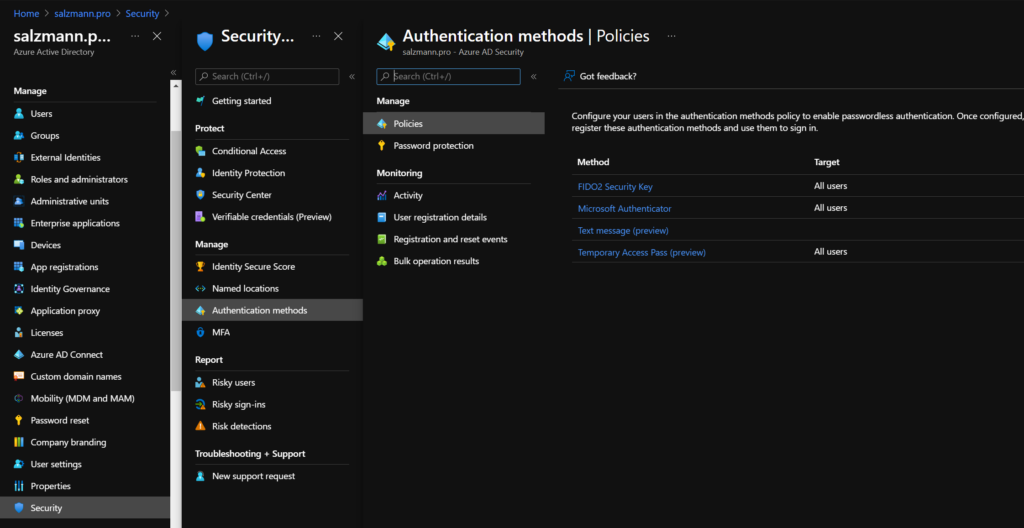
Im Azure AD muss nur die Authentifizierungs-Methode FIDO2 Security Key für eine bestimmte Gruppe oder alle Benutzer aktiviert werden.
Hierzu navigieren wir im Portal zu Authentication methods - Microsoft Azure:
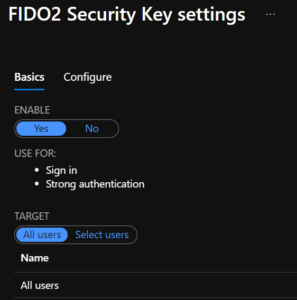
ℹ️ Im Falle einer ersten Aktivierung ist die Option für das Benutzer Enrollment sofort verfügbar.
Windows, lokal für Login
Lokal auf den Windows Rechnern können wir via OMA-Uri folgende Policy verteilen, um den Login mit einer Smart Card zu aktivieren.
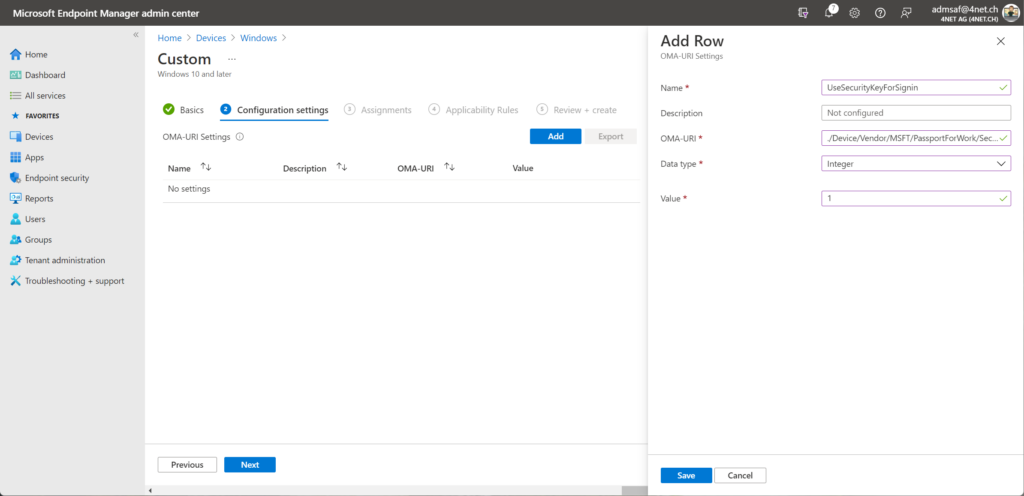
| Setting | Wert |
|---|---|
| Name | UseSecurityKeyForSignin |
| Description | nicht zwingend nötig |
| OMA-Uri | ./Device/Vendor/MSFT/PassportForWork/SecurityKey/UseSecurityKeyForSignin |
| Data type | Integer |
| Value | 1 |
Benutzer Enrollment
YubiKey Bio einrichten
Vorausgesetzt der Benutzer hat bereits ein Passwort und MFA konfiguriert, kann er den Stick wie folgt konfigurieren:
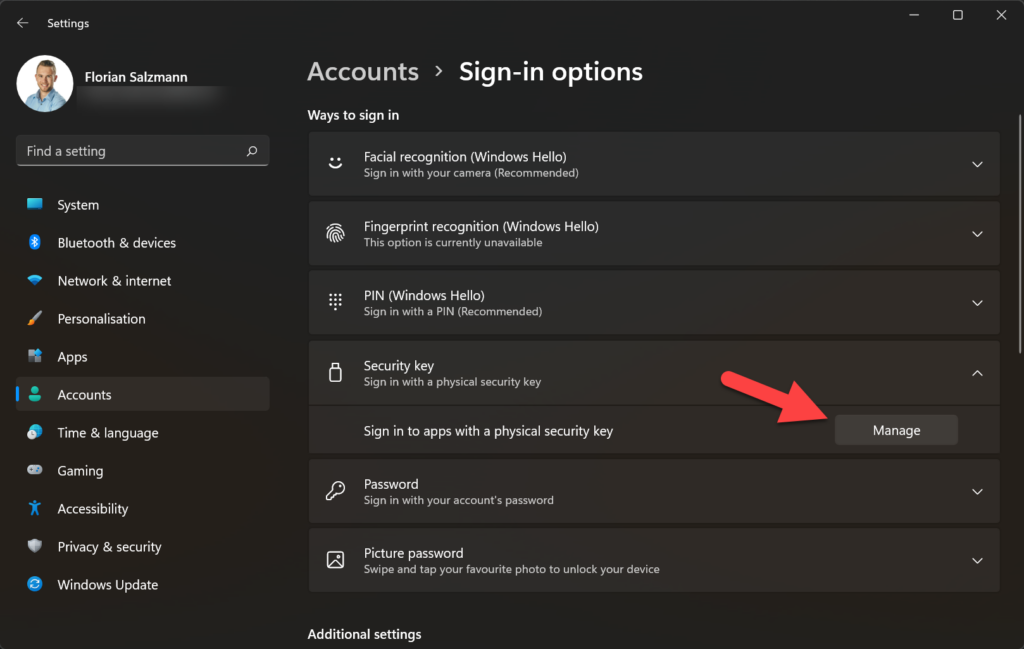
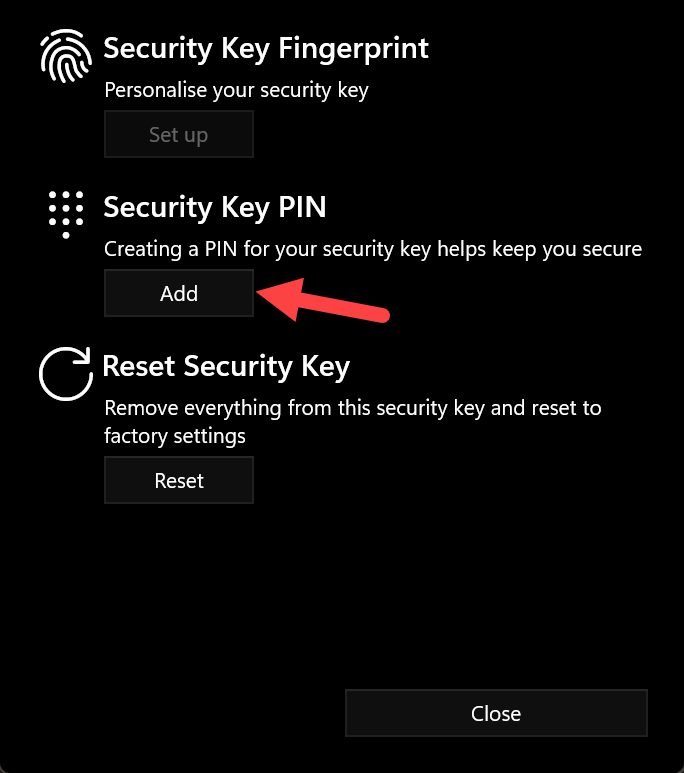
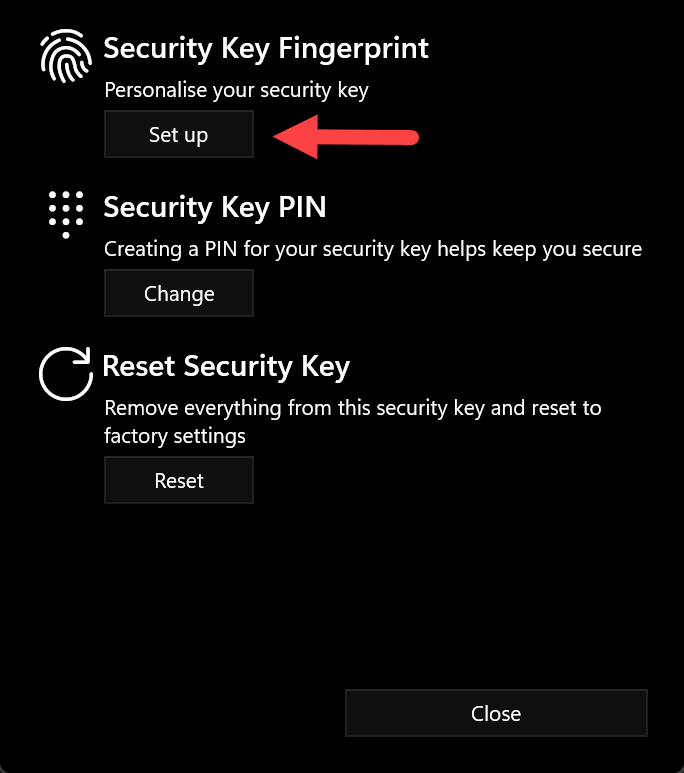
- In den Windows Einstellungen Unter Sign-in Optionen den Security Key konfigurieren
- Am besten den Stick von Anfang an einstecken.
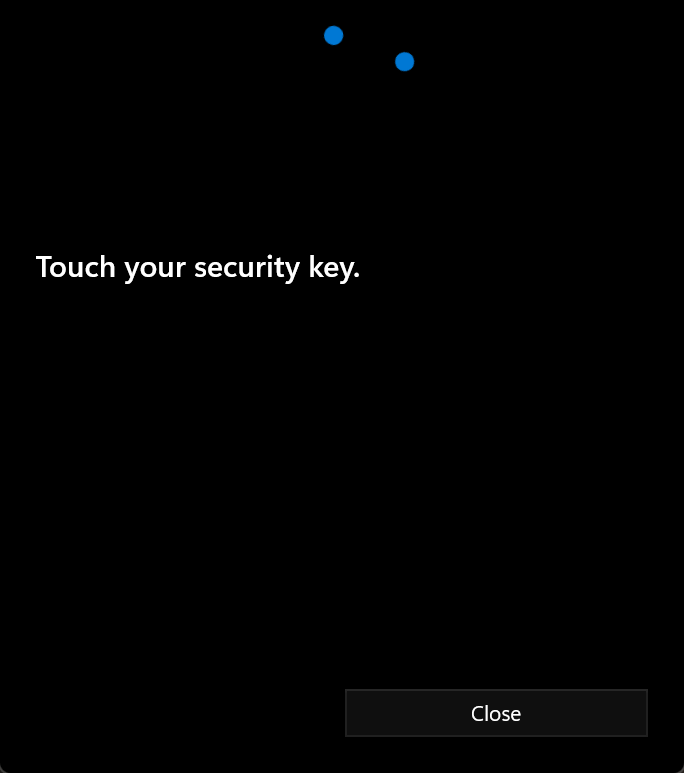
- Vorausgesetzt der Stick wird erkannt, muss er einmalig auf dem Fingerprint Sensor angetippt werden und ein PIN kann gesetzt werden.
- Ist der PIN gesetzt, kann der oder die Finger eingelesen werden.
- Durch das Setzten des PIN wird die Fingerabdruck Funktion freigeschaltet.
ℹ️ Einen schönes Vide bietet yubico selbst, welches für Benutzer sehr hilfreich sein kann: https://youtu.be/Fp96iTxk0RU
Ist die Option nicht verfügbar, kann sie wie in vergangenen Beitrag beschrieben aktiver werden: Windows Hello | scloud
YubiKey für Azure AD nutzen (inkl. Windows Hello for Business Login)
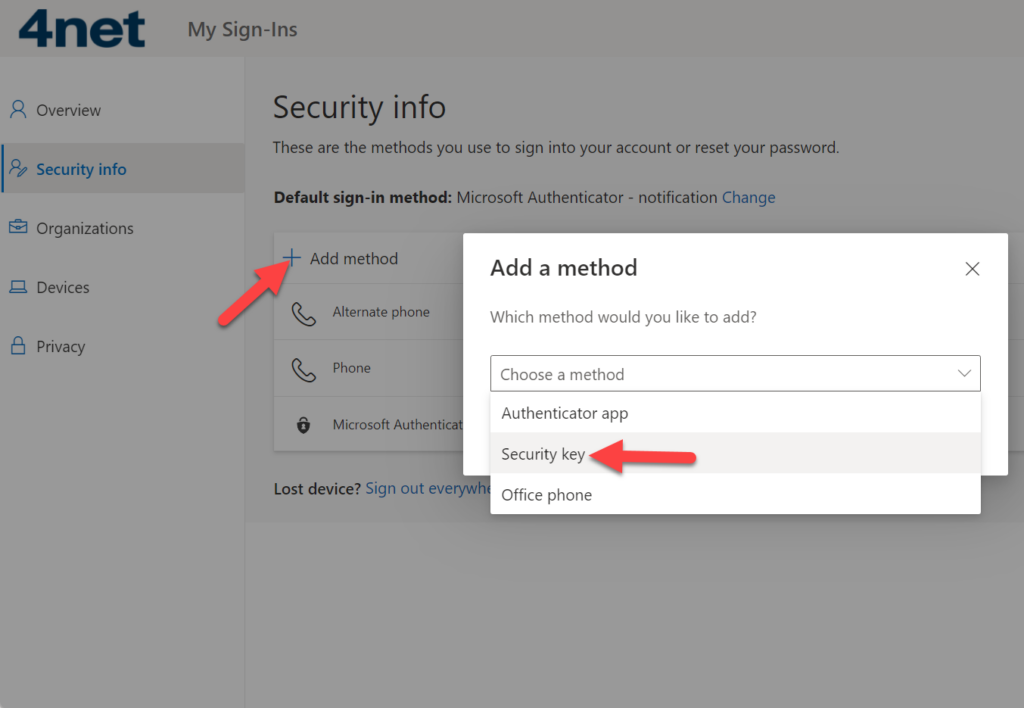
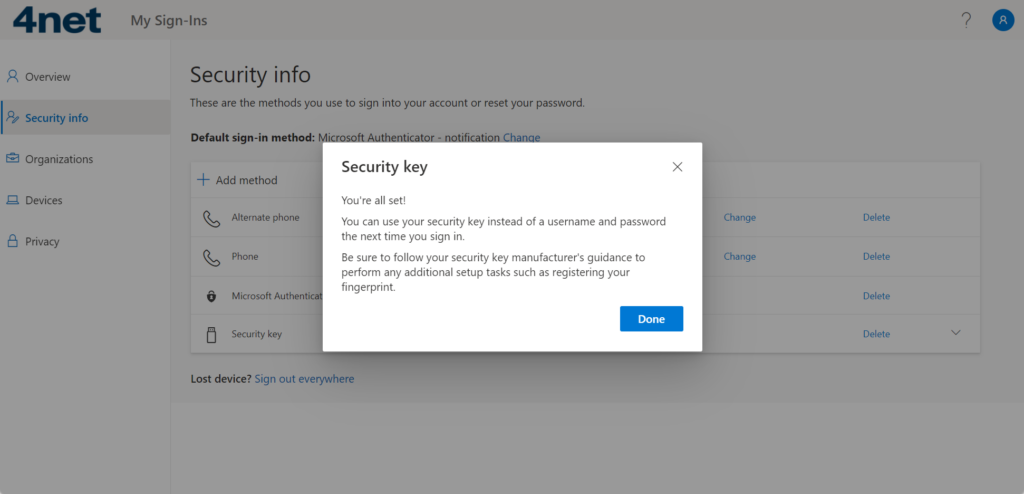
- Der YubiKey Bio (oder auch andere Modelle) können via MFA Setup (https://aka.ms/setupmfa) hinzugefügt werden.
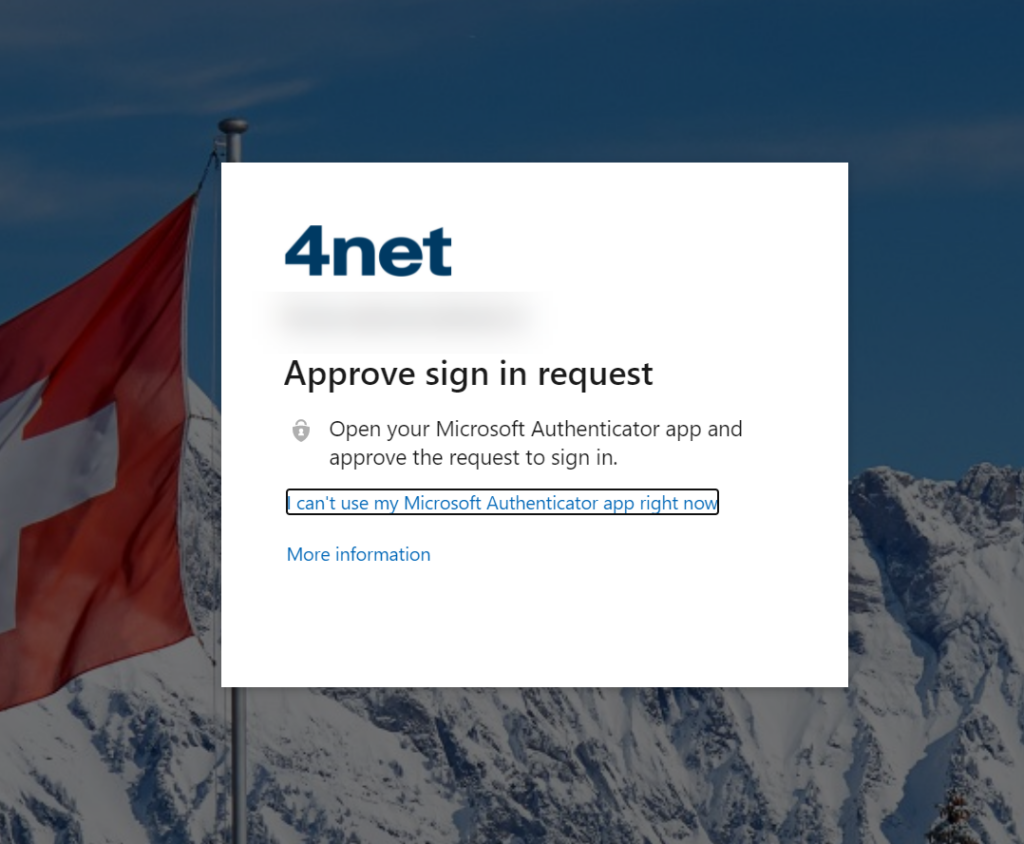
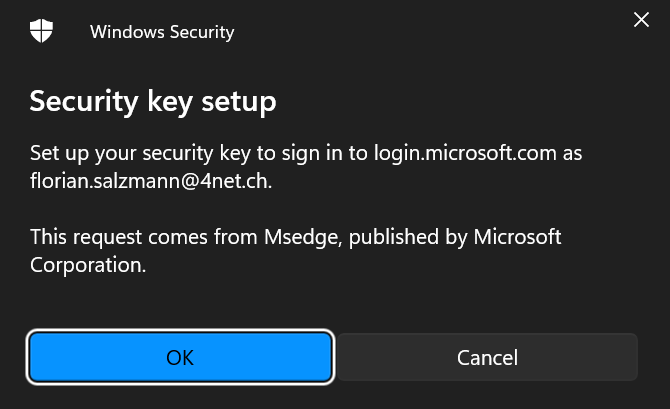
Ist MFA aktiv, muss der zweite Faktor erneut bestätigt werden.
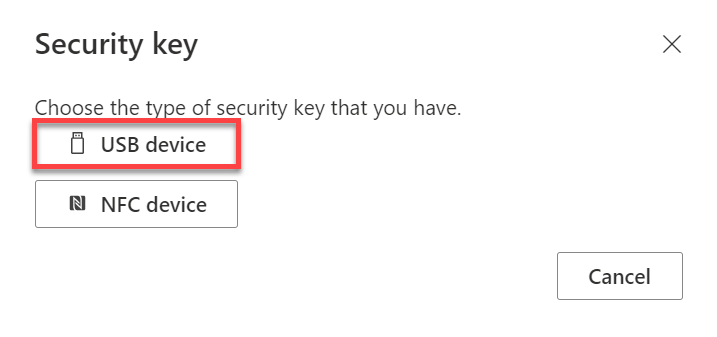
- Anschliessend kann "USB device" ausgewählt werden und das lokale Windows Kontextmenu öffnet sich.
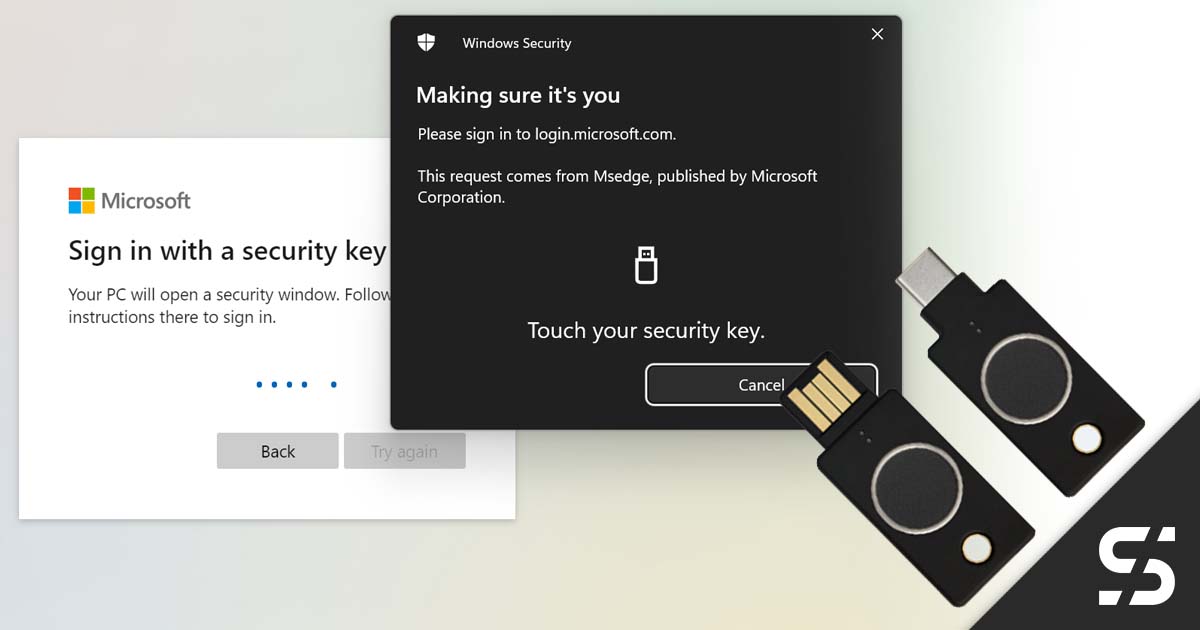
Die angezeigten Windows Security Hinweise können wir alle bestätigten.
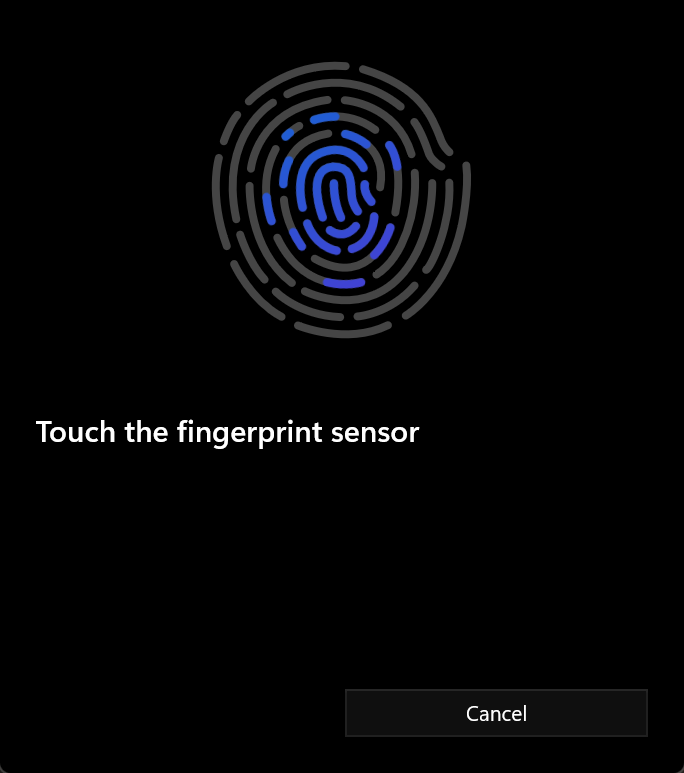
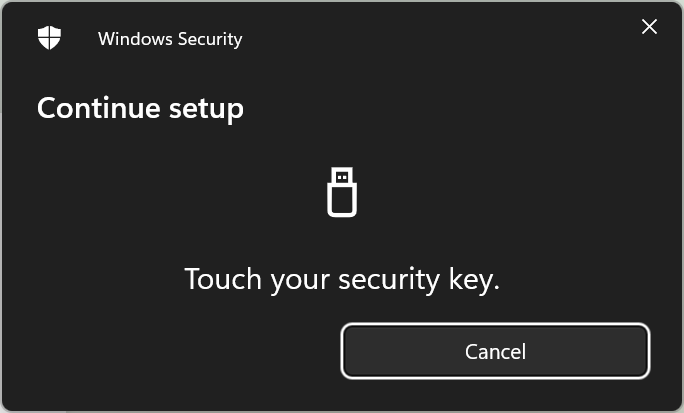
- Nach den Hinweisen muss der Key nur noch mit dem eigenen Finger (Code bei YubiKeys ohne Scanner) bestätigt werden.
Login mit YubiKey (Benutzer Sicht)
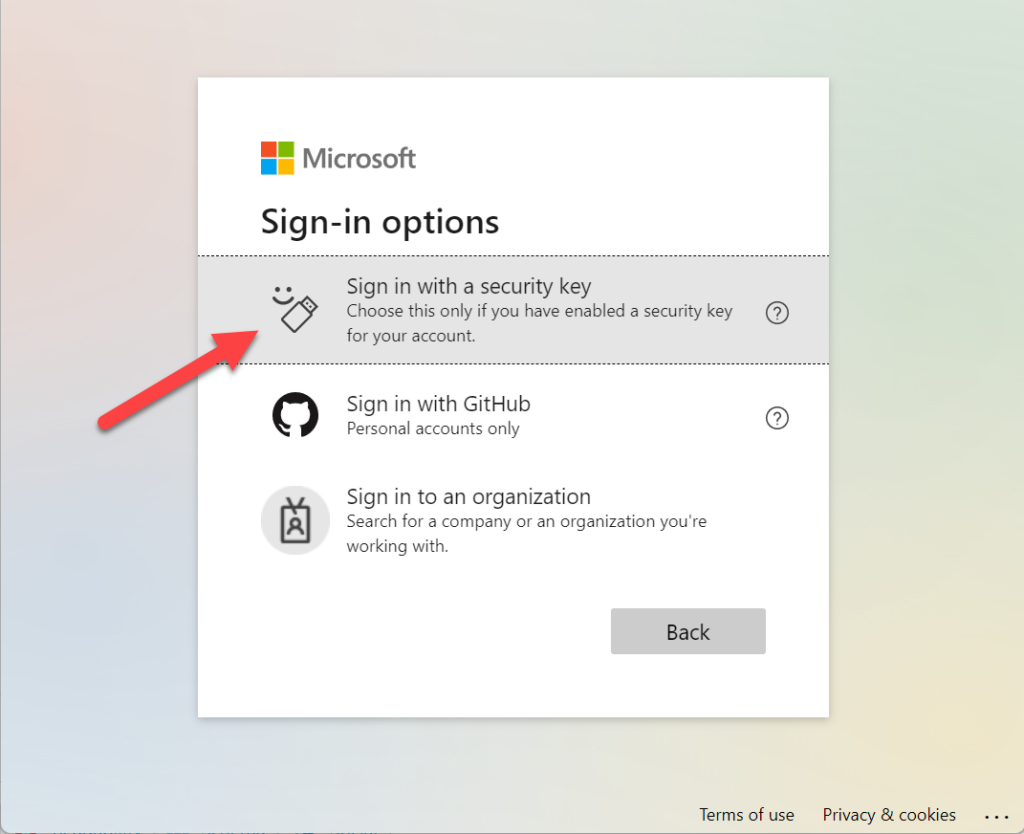
Login via portal.office.com
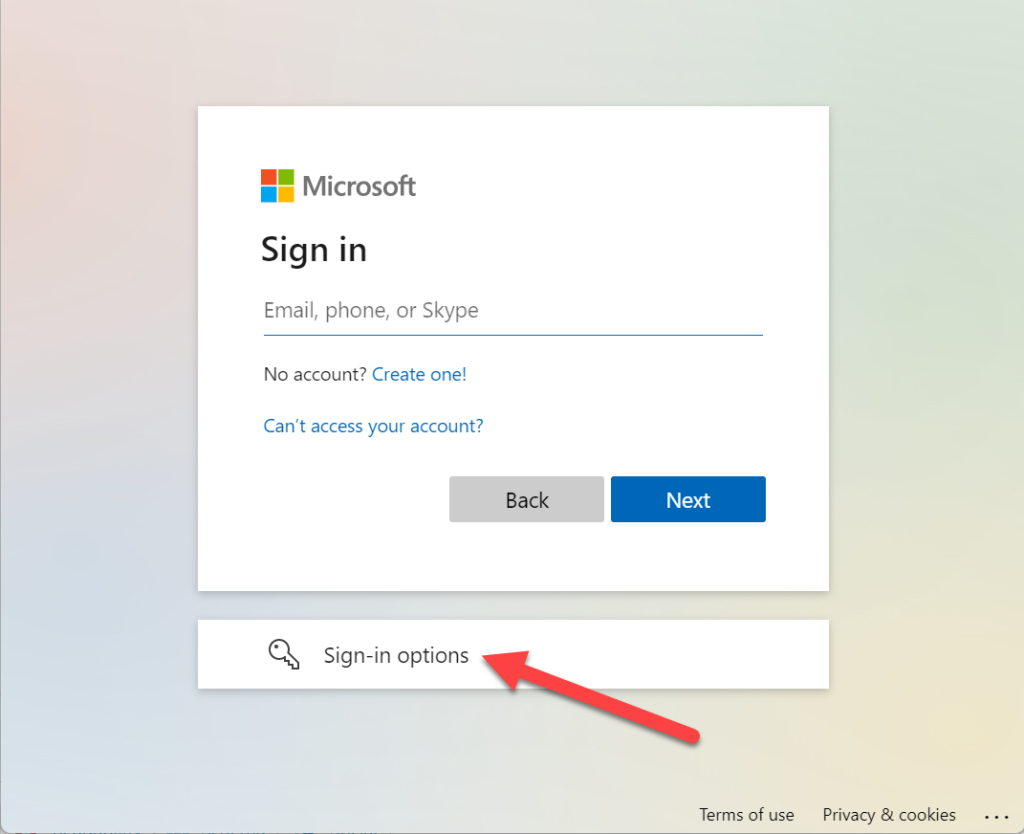
Der Login via Browser ist sehr einfach und intuitiv, es wird weder ein Username noch Passwort benötigt. Man schliesst lediglich den YubiKey Bio an, wählt die Security Key Authentifizierung und betätigt den Fingerprint.
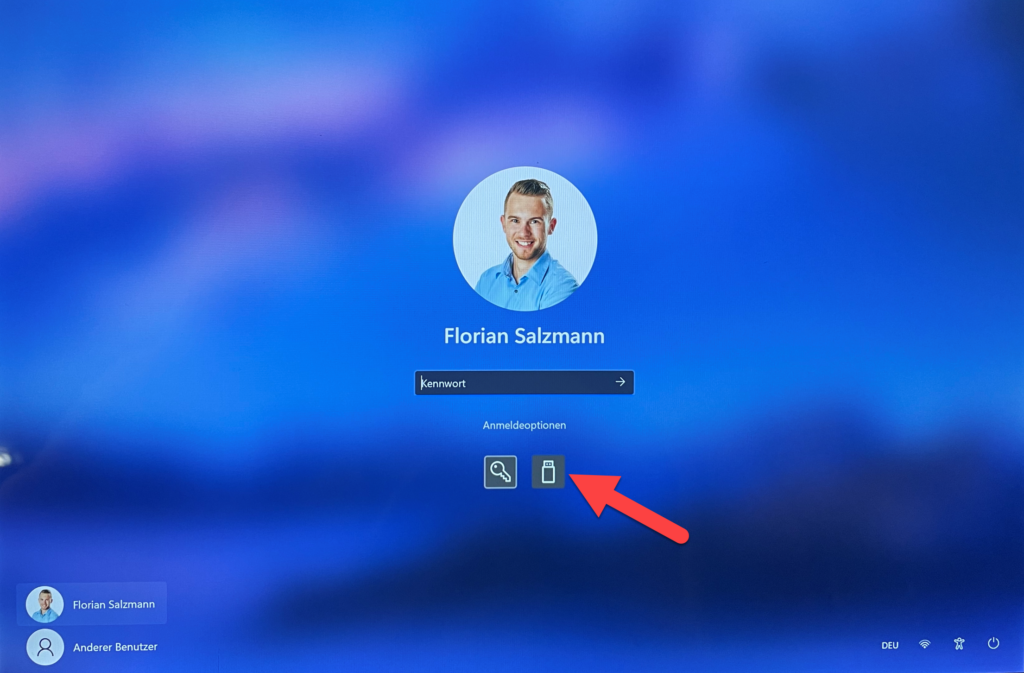
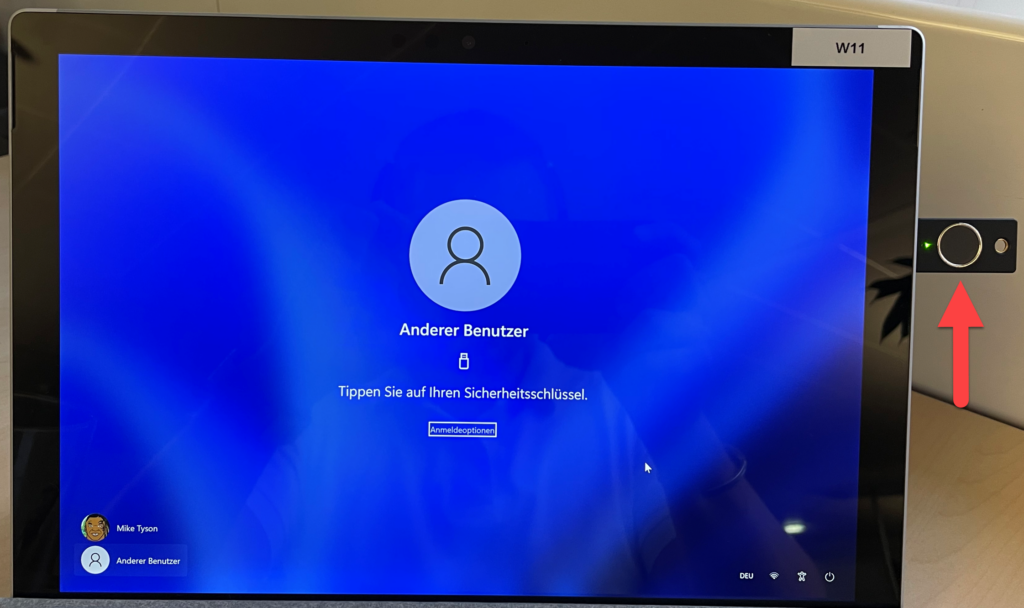
Login an einem Windows PC (AAD Joined)
Meistens wird der Key direkt erkannt, ist dies nicht der Fall, muss in den Anmeldeoptionen die Option "FIDO-Sicherheitsschlüssel" ausgewählt werden.
Erkenntnisse
Der Key ist sehr zuverlässig und einfach zu bediene. Ehrlich gesagt musste ich mich etwas dazu zwingen, ihn für eine Woche als einzige Login Methode zu verwenden. Hauptgrund dafür ist, dass ich an meinem Gerät Windows Hello for Business konfiguriert habe und für Online Logins MFA via Authenticator nutze. Durch das kleine Experiment kann ich aber die Zuverlässigkeit bestätigen.
Für einen Benutzer, der entweder kein Smartphone hat, an einem geteilten Gerät arbeitet oder oft den Standort wechselt, sehe ich die Lösung mit einem YubiKey BIO (FIDO2) aber definitiv als sehr praktikabel uns sicher. Gerade der Fingerabdruck bietet eine sehr bequeme und sichere Authentifizierungsmethode. Durch den Fingerabdruck sollte auch kein Mitarbeiter sein PIN vergessen können 😉.







Why am I only able to configure my Yubikey with Azure MFA with both the PIN and the fingerprint?
I am not able to enroll my Yubikey without first entering a PIN. Then, once configured, any MFA challenges, both the PIN and the fingerprint are required.